Did someone else notice that #Malpedia is offline? Or is this just the case for me?
You can now check your strings in #malcat against an online library of #Malpedia FLOSSed strings. Just copy this plugin:
https://github.com/malpedia/malpedia-flossed?tab=readme-ov-file#plugin-for-malcat
A very nice dataset from Malpedia with all the deobfuscated strings from their dataset. The repository contains the result of the FLARE FLOSS tool applied to all unpacked and dumped samples in Malpedia.
🔗 https://github.com/malpedia/malpedia-flossed
#dataset #opensource #malpedia #infosec #research #malware #opendata
GitHub - malpedia/malpedia-flossed: FLARE floss applied to all unpacked+dumped samples in Malpedia, pre-processed for further use.
FLARE floss applied to all unpacked+dumped samples in Malpedia, pre-processed for further use. - GitHub - malpedia/malpedia-flossed: FLARE floss applied to all unpacked+dumped samples in Malpedia, ...
I wrote a blog on new features in the IDA plugin for #MCRIT, most notably being able to query basic blocks or the whole currently viewed function against a dataset like #Malpedia in mere seconds, making it viable as a live companion while analyzing malware.
https://danielplohmann.github.io/blog/2023/08/02/mcrit_blocks.html
A great resource on finding malware groups information and analysis is #malpedia : https://malpedia.caad.fkie.fraunhofer.de/
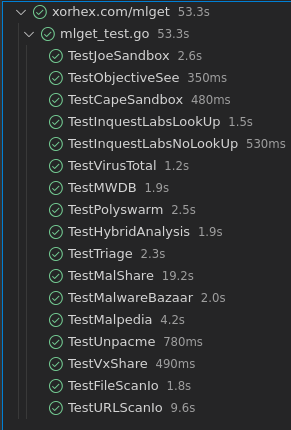
#mlget has been updated. Grab the latest copy from: https://github.com/xorhex/mlget/releases
Features Added:
- Downloaded file is hashed and compared against the hash requested. Hopefully this will help detect when APIs change.
- #URLScanIO source added! Making this the 16th source queried!!
Bug Fixes:
- #Malpedia works again
Breaking Changes:
- If using #JoeSandbox, delete and recreate the config entries as the URL was updated to be inline with how the rest of the URLs are formatted (/v2 was moved from the code to the config)
Other Changes:
- Fix minor typos and remove #AnyRun reference from the help menu as that option is not available yet.
Some additions, improvements, and fixes coming to #mlget soon.
https://github.com/xorhex/mlget
Mlget is a #malware downloader, allowing you to download from the following services:
#capesandbox
#filescanio
#hybridanalysis
#inquests
#joesandbox
#malpedia
#malshare / @malshare
#malwarebazaar
#mwdb
#objectivesee
#polyswarm
#triage
#unpacme
#urlscanio <-- NEW ADDITION COMING
#vt /#virustotal
#vxshare / @VXShare
It can also download and automatically upload to an MWDB instance of your choice.