Posts are my own and do not reflect my employer.
| mlget | http://github.com/xorhex/mlget |
| blog | https://blog.xorhex.com |
| twittodon | https://twittodon.com/share.php?t=xorhex&[email protected] |
| mlget | http://github.com/xorhex/mlget |
| blog | https://blog.xorhex.com |
| twittodon | https://twittodon.com/share.php?t=xorhex&[email protected] |
Wake up binjas, new Binary Ninja 5.3.9757 stable just dropped. No functionality this time (head over to dev for that!) but lots of stability fixes for the appropriately named stable branch:
We offer a free and simple API endpoint to grab all the hostnames for a domain based on the certificate transparency logs: https://ctl.shodan.io/
Sample Python code available in the Shodan book: https://book.shodan.io/developer-apis/certificate-transparency/
(considering *I* know how to track these... and have considered writing software to see who/what is constantly in the neighborhood or just driving by... it' not difficult to see how a company would attempt to commercialize this)
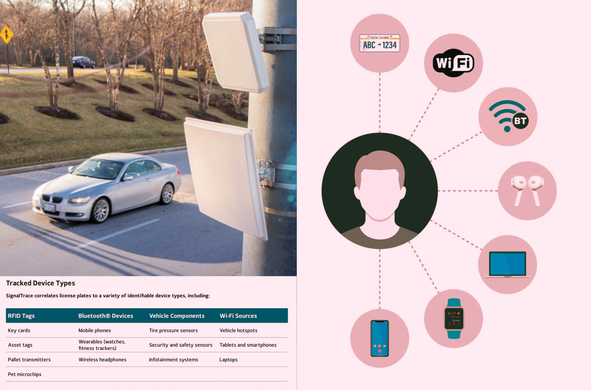
"...SignalTrace “bridges license plate recognition data with sensor-captured device identifiers—such as those from mobile phones, Bluetooth wearables, and vehicle systems—to create a unique, trackable ‘electronic fingerprint’ for investigative use,” according to a product sheet describing the tool, written by surveillance company Leonardo, which advertises SignalTrace.
The sort of data Leonardo says SignalTrace can sweep up includes the RFID tags in key cards and pet microchips; devices with Bluetooth such as wireless headphones, fitness trackers, and mobile phones; components of a car like tire pressure sensors and infotainment systems; and Wi-Fi sources such as vehicle hotspots and laptops, according to the product sheet..."
Mini Shai-Hulud/Miasma/Hades are now targeting bioinformatics and MCP developers in a newer PyPI wave.
We found 23 newly compromised PyPI package-version artifacts using multiple execution paths.
The payload also includes a fake prompt-injection header at the top of _index.js to interfere with LLM-based malware triage before scanners reach the obfuscated code.
Full breakdown:
https://socket.dev/blog/mini-shai-hulud-miasma-and-hades-worms-target-bioinformatics-and-mcp-developers-via-malicious
SignalTrace "links devices that regularly travel together, correlating them to license plate." It is a surveillance product that will sweep up and add all sorts of Bluetooth and other data to license plate readers, linking specific devices—and people—to cars.
SignalTrace “links devices that regularly travel together, correlating them to license plate.” It is a surveillance product that will sweep up and add all sorts of Bluetooth and other data to license plate readers, linking specific devices—and people—to cars.
Do you like T-shirts? How about coffee mugs?
You can support IFIN's mission and also get some cool merch! All proceeds go directly to operational costs and building our capacity to produce and share free cyber threat intelligence resources.
(stickers coming soon)
Evan is presenting at RVAsec tomorrow at 1pm! Be sure to check out his talk and grab some Zeek stickers.
Other community news & more in our newsletter: https://community.zeek.org/t/zeek-newsletter-issue-63-may-2026/7994/1
Our team at Amnesty Security Lab is hiring for a technologist to help protect civic space from unlawful surveillance. The work is varied, blending digital forensics research with threat intelligence, industry collaboration and community work.
We are encouraging candidates of all backgrounds to apply - come fight bad guys with us.
https://careers.amnesty.org/jobs/vacancy/technologist-4246/4274/description/