🚑 Limited threat visibility slowed triage and response at Health Shared Services, a Canada-based healthcare organization supporting 130K+ endpoints.
See how #ANYRUN changed their SOC workflow (spoiler alert: it reduced MTTR/MTTD and alert fatigue) 👇
https://any.run/cybersecurity-blog/healthcare-success-story/?utm_source=mastodon&utm_medium=post&utm_campaign=healthcare_success_story&utm_term=240326&utm_content=linktoblog
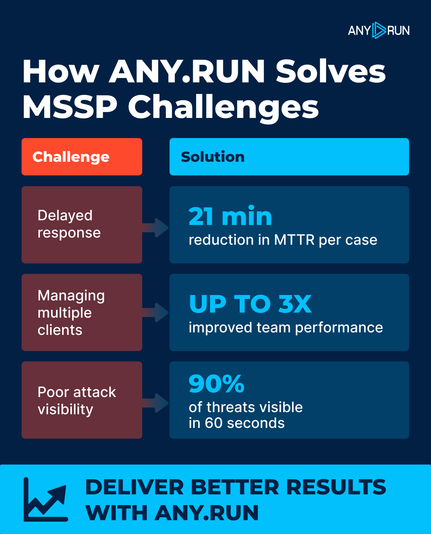
📈 MSSP growth brings higher alert volume and stricter SLAs.
Unifying detection, enrichment, and reporting with #ANYRUN helps teams support more clients while keeping service quality consistent.
⚡️ See how #ANYRUN strengthens MSSP operations at scale: https://any.run/mssp/?utm_source=mastodon&utm_medium=post&utm_campaign=mssp_challenges_solved&utm_term=240326&utm_content=linktomssp
🚨 𝗦𝗩𝗚 𝗦𝗺𝘂𝗴𝗴𝗹𝗶𝗻𝗴 𝗖𝗮𝗺𝗽𝗮𝗶𝗴𝗻 𝗛𝗶𝘁𝘀 𝗖𝗼𝗹𝗼𝗺𝗯𝗶𝗮𝗻 𝗢𝗿𝗴𝗮𝗻𝗶𝘇𝗮𝘁𝗶𝗼𝗻𝘀
We’re seeing a surge in a #phishing campaign targeting government, finance, oil and gas, and healthcare sectors in Colombia ⚠️
Attackers distribute Spanish-language emails with an attached SVG file. The file is not a static image but an active SVG containing embedded JavaScript that uses SVG smuggling to reconstruct the next stage locally via a blob URL, without fetching a payload from external resources.
The browser then generates an intermediate HTML lure that mimics document preparation, and from embedded data creates a password-protected ZIP archive for the user to open.
❗️ This kind of attack can blur early-stage visibility for SOC teams. SVG smuggling, blob objects, and legitimate Windows components break the compromise into weak signals, making detection and investigation harder in the early stages.
⚡ #ANYRUN Sandbox allows analysts to quickly reconstruct 𝘁𝗵𝗲 𝗳𝘂𝗹𝗹 𝗲𝘅𝗲𝗰𝘂𝘁𝗶𝗼𝗻 𝗰𝗵𝗮𝗶𝗻:
SVG smuggling ➡️ Blob-based HTML lure ➡️ Password-protected ZIP ➡️ Notificacion Fiscal.js (launcher / execution handoff) ➡️ radicado.hta (dropper) ➡️ J0Ogv7Hf.ps1 (script-based RAT / Vjw0rm-like implant) ➡️ C2 communication
✅ This helps security teams connect scattered artifacts faster, expose hidden delivery stages, and confirm malicious activity before the attack moves further.
👨💻 Learn how #ANYRUN helps detect complex threats faster: https://any.run/features/?utm_source=mastodon&utm_medium=post&utm_campaign=svg_smuggling_campaign&utm_term=230326&utm_content=linktosandboxlanding
🏦 Protect critical infrastructure and customer trust.
#ANYRUN supports triage, continuous monitoring, and threat hunting while keeping sensitive data under strict control.
✅ Identify up to 58% more threats, reduce Tier 1 workload, and cut MTTR: https://any.run/by-industry/finance/?utm_source=mastodon&utm_medium=post&utm_campaign=solving_finance_challenges&utm_term=190326&utm_content=linktofinance
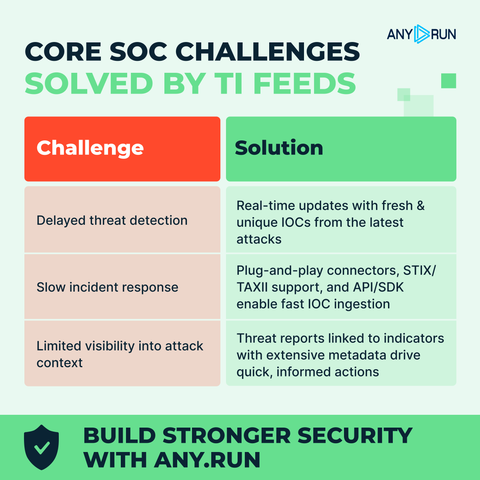
⚠️ Slow detection, delayed response, and limited context keep SOCs reactive.
#ANYRUN TI Feeds bring fresh IOCs from real attacks into SIEM/XDR, helping spot threats earlier and move to proactive defense.
👨💻 See how TI Feeds work in real SOC workflows: https://any.run/threat-intelligence-feeds/?utm_source=mastodon&utm_medium=post&utm_campaign=soc_challenges_feeds&utm_term=190326&utm_content=linktofeedslanding
❗️ SOCs & MSSPs waste time enriching alerts by hand, slowing response.
Connect #ANYRUN Sandbox with your Microsoft Sentinel workspace to detect and contain attacks earlier with actionable threat insights ⚡️
Set it up in minutes: https://any.run/cybersecurity-blog/malware-sandbox-ms-sentinel-connector/?utm_source=mastodon&utm_medium=post&utm_campaign=anyrun_sandbox_sentinel&utm_term=180326&utm_content=linktoblog
When alerts lack context, triage slows down and MTTR grows ⏳
#ANYRUN’s integration with MISP lets teams validate alerts with behavior-based evidence, while TI Feeds enrich сases with IOCs from live attacks
Hit SLA targets and keep operations efficient 👇
https://any.run/cybersecurity-blog/anyrun-sandbox-misp-integration/?utm_source=mastodon&utm_medium=post&utm_campaign=anyrun_misp_integration&utm_term=170326&utm_content=linktoblog
What an amazing time at RootedCON 2026 🇪🇸
It was great to connect with the cybersecurity community and share how #ANYRUN helps teams make faster decisions.
See the full recap and new capabilities for greater SOC efficiency ⬇️
https://any.run/cybersecurity-blog/anyrun-rootedcon-2026/?utm_source=mastodon&utm_medium=post&utm_campaign=rootedcon_2026&utm_content=linktoblog&utm_term=160326
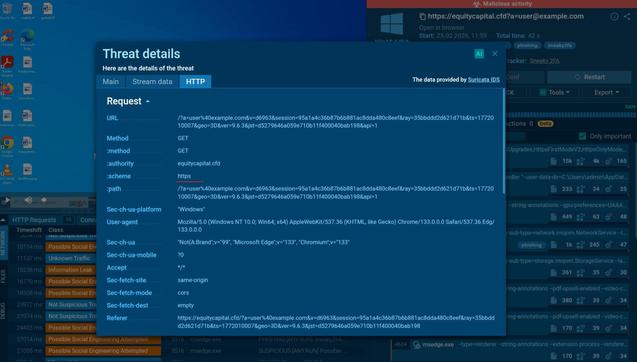
🎣 #Salty2FA relies on encrypted HTTPS communication for fake login pages, redirect flows, and data exfiltration. That’s why it often looks harmless at first glance, delaying confirmation and increasing the risk of credential compromise.
The full phishing flow becomes visible when HTTPS traffic is automatically decrypted in #ANYRUN Sandbox: https://app.any.run/tasks/73fb8a10-2721-4da4-9f9b-a340a6eac370?utm_source=mastodon&utm_medium=post&utm_campaign=salty_ssl_decryption&utm_term=120326&utm_content=linktoservice
👨💻 Learn how #ANYRUN improves phishing detection for SOC teams: https://any.run/cybersecurity-blog/automatic-ssl-decryption/?utm_source=mastodon&utm_medium=post&utm_campaign=salty_ssl_decryption&utm_term=120326&utm_content=linktoblog
🚨 𝗦𝗽𝗼𝘁 𝗜𝘁 𝗘𝗮𝗿𝗹𝘆: 𝗖𝗿𝗲𝗱𝗲𝗻𝘁𝗶𝗮𝗹 𝗧𝗵𝗲𝗳𝘁 𝗕𝗲𝗵𝗶𝗻𝗱 𝗙𝗮𝗸𝗲 𝗣𝗗𝗙𝘀
Attackers disguise #phishing HTM/HTML email attachments as PDF files. In the observed case, pdf.htm displays a fake login page and sends entered credentials in JSON via HTTP POST to the Telegram Bot API, enabling account takeover and access to internal systems.
Some samples use obfuscated scripts, making the exfiltration logic harder to spot ❗️
⚡️ #ANYRUN Sandbox exposed phishing behavior in under 60 seconds, revealing the outbound network activity, loaded scripts, and file contents, helping analysts accelerate triage and reduce unnecessary escalations.
🎣 See the analysis session and collect #IOCs to speed up detection and cut MTTR: https://app.any.run/tasks/3a6af151-cf57-461f-b600-19c39fdfcce6?utm_source=mastodon&utm_medium=post&utm_campaign=html_pdf_phishing&utm_content=linktoservice&utm_term=110326
🔍 Find similar cases and pivot from IOCs using this TI Lookup search query: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=html_pdf_phishing&utm_content=linktotilookup&utm_term=110326#%7B%2522query%2522:%2522filePath:%255C%2522.pdf.html$%255C%2522%2520OR%2520filePath:%255C%2522.pdf.htm$%255C%2522%2522,%2522dateRange%2522:180%7D
👨💻 Learn how #ANYRUN Sandbox helps SOC teams detect complex threats faster: https://any.run/features/?utm_source=mastodon&utm_medium=post&utm_campaign=html_pdf_phishing&utm_term=110326&utm_content=linktosandboxlanding