"🍎 macOS Malware 2023: Navigating the New Threat Landscape 🌐"
Apple's XProtect recently updated to version 2173, introducing rules for Atomic Stealer and Adload. However, 2023 has unveiled novel methods to compromise Macs, leaving users vulnerable unless additional protective measures are taken. Key insights:
Shift in Malware Behavior: Many macOS malware families in 2023 have ditched persistence. Infostealers, for instance, achieve their goals in a single execution, stealing user data and then transmitting it to a remote server. 📥🔓
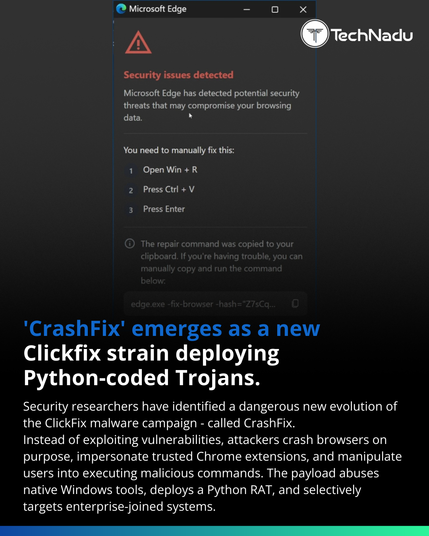
Sophisticated Social Engineering: Threat actors are employing advanced social engineering tactics. RustBucket malware, for example, lured victims with a business deal, urging them to download a 'proprietary' PDF viewer, which in reality was malware. 🎣📄
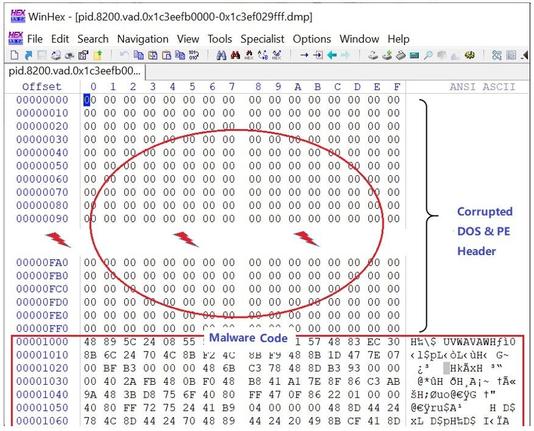
Public Offensive Security Tools: Tools like Geacon, which wraps Cobalt Strike capabilities, are now being seen in macOS malware. Open-source red teaming tools like Mythic and Poseidon have also been spotted in recent campaigns. 🛠️🔥
LOLBins Techniques: "Living off the orchard" techniques are on the rise in macOS. Built-in tools like system_profiler, sw_vers, and curl are being exploited for malicious purposes. 🌳🔧
Abusing Open Source Software: JokerSpy malware, discovered in July 2023, began its infection through a trojanized QR code generator, QRLog. This malware was found in enterprise breaches, including a major cryptocurrency exchange. 🔄💼
Complex Multi-Stage Malware: The Smooth Operator campaign, a sophisticated supply chain attack, compromised businesses via 3CX's call routing software client. The malware was designed for stealth, gathering limited data and then self-deleting. 📞🕵️
While Apple is enhancing its malware detection capabilities, third-party solutions are still crucial for comprehensive protection against both common and advanced threats. SentinelOne offers a robust platform for macOS threat detection and remediation. 🛡️💻
Source: SentinelOne
Tags: #macOS #Malware #CyberSecurity #XProtect #Infostealers #SocialEngineering #OffensiveSecurity #LOLBins #OpenSource #SentinelOne 🌍🔒🖥️