| Website | https://huntress.com |
| https://twitter.com/huntresslabs | |
| https://www.linkedin.com/company/huntress-labs/ |
Huntress
- 625 Followers
- 6 Following
- 67 Posts
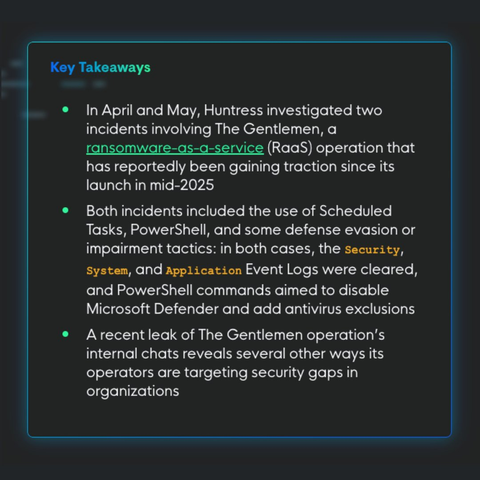
A leak of The Gentlemen's internal database added even more context, giving defenders a rare look at how the operation runs and what vulnerabilities they're actively targeting.
Lindsey O'Donnell-Welch and Harlan Carvey share the details:
https://www.huntress.com/blog/the-gentlemen-ransomware-defense-evasion-ttps
What they didn't count on? The breadcrumbs they left behind.
Incomplete clearing and leftover PowerShell event logs gave our analysts enough to piece the story together.
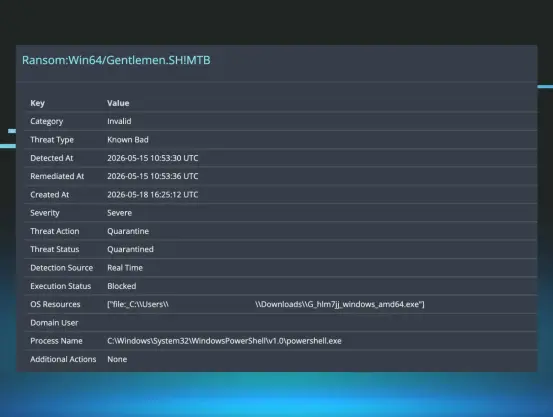
In both cases, the attackers followed a similar playbook.
When Defender blocked the first attempt to launch the encryptor, they didn’t give up. They cleared event logs, ran PowerShell commands to disable Defender and add exclusions, and came back for round two.
An unknown threat actor is abusing a remote management tool called #TiFLUX as an initial access vector, targeting a broad range of potential victims by email. The attacks using this Brasil-originated commercial utility began in February, but really ramped up in April and the beginning of this month.
The lures employ a variety of #spam tropes, including bogus event invitations and business invoices/bills.
TiFLUX seems uniquely vulnerable to this kind of abuse; The installer package also installs an old version of UltraVNC as well as a vulnerable #loldriver that can elevate privileges. Weirdest of all, the attackers are also using this RMM to deploy other heavily-abused RMMs, including #Splashtop and #ScreenConnect to the devices that get hit. Those RMMs are connecting to IP addresses associated with known bulletproof hosts.
This is my first post at the @huntress blog: https://www.huntress.com/blog/tiflux-rmm-install
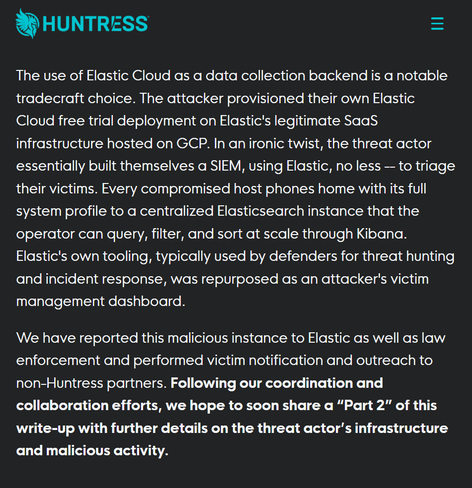
1. Zoho Assist RMM
2. QEMU & Cloudflared
3. Velociraptor for C2
and a wild story (to tell more about soon 😎): an attacker controlled Elastic stack for exfil 🔗👇
Check out @hrbrmstr today on @huntress's Tradecraft Tuesday at 1pm ET to chat about all things #React2Shell. 🤘