The Exploiting Reversing Series (ERS) currently features 945 pages of exploit development based on real-world targets:
[+] ERS 08: https://exploitreversing.com/2026/03/31/exploiting-reversing-er-series-article-08/
[+] ERS 07: https://exploitreversing.com/2026/03/04/exploiting-reversing-er-series-article-07/
[+] ERS 06: https://exploitreversing.com/2026/02/11/exploiting-reversing-er-series-article-06/
[+] ERS 05: https://exploitreversing.com/2025/03/12/exploiting-reversing-er-series-article-05/
[+] ERS 04: https://exploitreversing.com/2025/02/04/exploiting-reversing-er-series-article-04/
[+] ERS 03: https://exploitreversing.com/2025/01/22/exploiting-reversing-er-series-article-03/
[+] ERS 02: https://exploitreversing.com/2024/01/03/exploiting-reversing-er-series-article-02/
[+] ERS 01: https://exploitreversing.com/2023/04/11/exploiting-reversing-er-series/
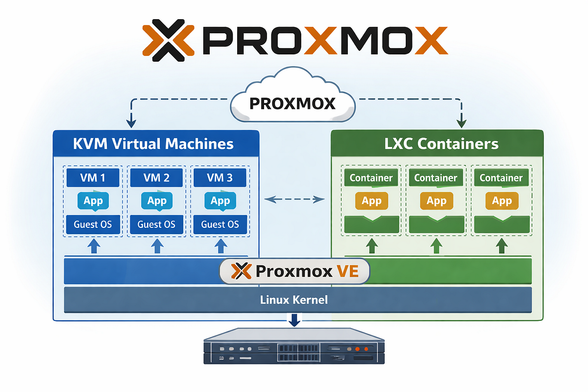
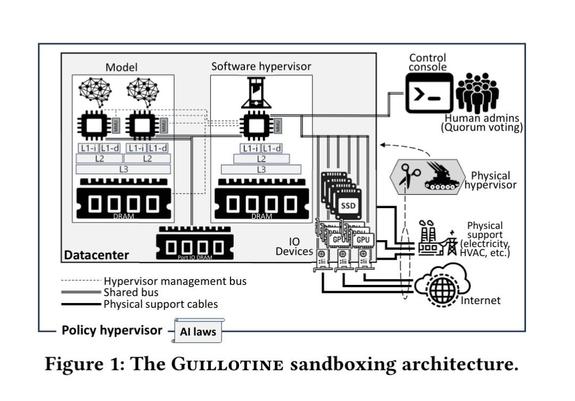
In the coming weeks, I will publish new articles covering exploration in areas such as Windows, Chrome, iOS/macOS, and hypervisors.
I sincerely hope these articles help other professionals define their own steps in this area.
Have a great day and enjoy reading.
#exploit #exploitation #windows #chrome #macOS #iOS #hypervisors #vulnerabilityresearch