#LinuxHacks #SecurityHacks #Hardwaretoken #Ssh #Sshkeys #TPM
#LinuxHacks #SecurityHacks #Hardwaretoken #Ssh #Sshkeys #TPM
Authenticate SSH with Your TPM
https://fed.brid.gy/r/https://hackaday.com/2026/04/11/authenticate-ssh-with-your-tpm/
Pünktlich zum #39C3 habe ich mein #Hardwaretoken #Howto erweitert um
#OpenSSH #Authentifizierung.
Ich zeige wie man sich an #SSH Servern einloggen kann mittels #FIDO2 Device Bound #Passkeys à la #Yubikey, #Nitrokey, #Token2 #Thetis etc.
Damit liegt der geheime Schlüssel im Passkey-Token und kann nicht ohne weiteres ausgelesen werden.
Außerdem zeige ich noch wie man einen 2. externen OpenSSH-Server nur für die Hardwaretoken konfiguriert.
Viel Spaß am Gerät
OpenSSH-Authentifizierung mittels Hardwaretoken (FIDO2 Device Bound Passkeys à la Yubikey, Nitrokey, Token2, Thetis etc.)
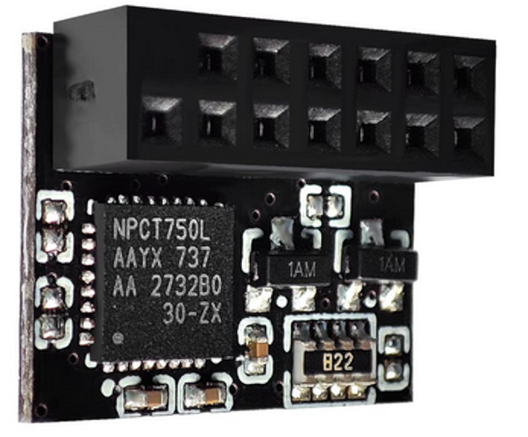
Voraussetzung Seit Version 8.2.0 unterstützt OpenSSH FIDO2 basierte Schlüssel, also Passkeys. Dieser Schlüssel kann dabei bequem als sog. device bound passkey (fürderhin Passkey genannt) auf einem Hardware-Token liegen. Der geheime Schlüssel kann dann nicht vom Token exportiert werden und ist somit vor Diebstahl geschützt. Das Hardwaretoken fungiert dann quasi als Hardware Security Module und schützt den geheimen Schlüssel. Eingesetzt werden kann dafür ein beliebiges FIDO2-konformes Token, z.B. ein Yubikey 5 oder Security Key, Token2 R3 oder ein Thetis Security Key.
Und weiter geht's bei meiner kleinen Reise durch die wunderbare Welt der #HardwareToken...
Die heutigen Logins am #openvpn und MS Dingens erfolgt mit dem zweiten #TOTP Faktor vom #yubikey. Somit habe ich nun 3 optionale Wege, an diesen Faktor zu kommen:
- #AndOTP
- #keepassxc
- yubikey
$ ykman oath accounts code pfsense
pfsense 416654 This is unfortunate because I received a pair of these recently that I've been meaning to take out of the package. I guess they won't be issuing recalls?
#securitykey #sidechannel #yubikey #yubikeys #hardwaretokens #hardwaretoken #cryptography #credentials #fido
https://security.stackexchange.com/questions/268557/how-are-hardware-keys-phishing-resistant-to-man-in-the-middle-attacks
#hardwaretoken #phishing #yubikey
I want to beef up my 2FA standards and I'm looking for a 2FA hardware token. The only one's I've ever used have been for work (RSA Tokens) but what else is out there? Better yet, what should I be looking for in a hardware token?

 👺
👺