#LinuxHacks #SecurityHacks #Hardwaretoken #Ssh #Sshkeys #TPM
#LinuxHacks #SecurityHacks #Hardwaretoken #Ssh #Sshkeys #TPM
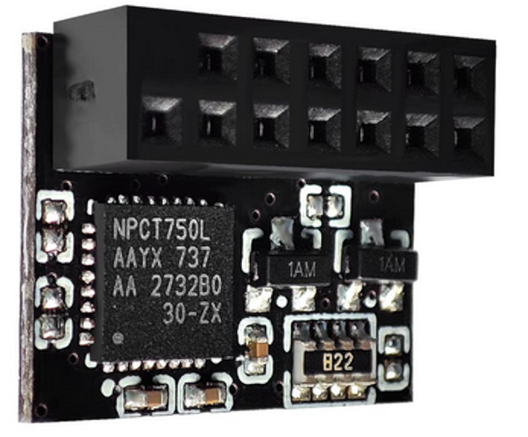
Authenticate SSH with Your TPM
https://fed.brid.gy/r/https://hackaday.com/2026/04/11/authenticate-ssh-with-your-tpm/
https://www.kenkoonwong.com/blog/parallel-computing/ #tinyPCs #supercomputer #SSHkeys #Skynet #HackerNews #ngated

Setting Up A Cluster of Tiny PCs For Parallel Computing - A Note To Myself | Everyday Is A School Day
Enjoyed learning the process of setting up a cluster of tiny PCs for parallel computing. A note to myself on installing Ubuntu, passwordless SSH, automating package installation across nodes, distributing R simulations, and comparing CV5 vs CV10 performance. Fun project!
Anyone got an idea how to do this:
- expose a user on a GNU/Linux system via ssh
- allow two keys access
- one is the “self” key, which should be allowed as-is
- the other is the “external” key, which triggers a password prompt
- otherwise, password login is not permitted
I know how to do most things of this, but not all at once (AuthenticationMethods is permitted in a Match block, but we cannot match on keys, we want access to the same user, and the “self” key can also be used (agent forwarding) from nōn-local addresses.
It seems like I’ll need a custom PAM module (arrrgh, I don’t want to write one of these) that asks for the password if key B is used (does SSH expose this to PAM?).
Anyone got a better idea?
Okay, here's the markdown version of your comprehensive guide to setting up SSH keys, formatted for readability.
https://www.mitim.net/2025/05/ssh-key-creation-and-usage?g=5
#SSH #Hardening #SSHkeys #CyberSecurity
https://infisical.com/blog/ssh-keys-dont-scale #SSHkeys #SSHcertificates #Cybersecurity #TechNews #Innovation #HackerNews #ngated
Learn how to use KDE Wallet and ksshaskpass for secure, seamless key management.
Read more on Medium: https://blog.schoenwald.aero/streamline-your-ssh-workflow-with-kde-plasmas-wallet-and-ksshaskpass-e22f49b6a07a
Suggestions for improvement are welcome, let's discuss!
#Linux #KDEPlasma #OpenSSH #SSHKeys #TechTips
Want to manage your deployments securely with DeployHQ? Learn how to create SSH keys from the command line using 5 different algorithms and configurations.
#SSHKeys #DeployHQ #Security #DevOps #ServerManagement
5 Ways to Create SSH Keys from the Command Line for DeployHQ
SSH keys are essential for securely connecting to your servers. DeployHQ allows you to upload custom SSH keys to manage your deployments. In this blog post, we'll explore 5 different ways to create SSH keys from the command line, each with its own algorithm and configuration options.
in case you may have not known, if you have a #yubikey or an #onlykey or something similar you can generate SSH keys that require them, for example:
`ssh-keygen -t ed25519-sk`
more info:
#linux #LinuxSecurity #CyberSecurity #Antivirus #Antimalware #LinuxServerProtection #LinuxDesktop #CyberProtection #TechSavvy #FirewallConfiguration #IntrusionDetection #RealTimeScanning #SSHKeys #StrongPasswords #RegularUpdates #LinuxSafety #SecureLinux
https://linuxexpert.org/how-to-protect-a-linux-server-or-desktop/