This Week In Security: Another Linux Exploit, Ubuntu Knocked Offline, Finals Interrupted, And Backdoored Tools
After the CopyFail vulnerability gave root access from any user on almost all distributions last week, this week we’ve got DirtyFrag. This chains the vulnerability in CopyFail (xfrm-ESP) and …

This Week In Security: Another Linux Exploit, Ubuntu Knocked Offline, Finals Interrupted, And Backdoored Tools
After the CopyFail vulnerability gave root access from any user on almost all distributions last week, this week we’ve got DirtyFrag. This chains the vulnerability in CopyFail (xfrm-ESP) and …

This Week In Security: State Malware, State Hardware Bans, And Stuxnet Before Stuxnet Was Cool
Making headlines everywhere is the CopyFail Linux kernel vulnerability, which allows local privilege escalation (LPE) from any user to root privileges on most kernels and distributions. Local privi…

This Week In Security: Annoyed Researchers, Dangling DNS, And Hacks That Could Have Been Worse
The author of the BlueHammer exploit, which was released earlier this month and addressed in the last Patch Tuesday, continues to be annoyed with the responses from the Microsoft security research …

This Week In Security: Annoyed Researchers, Dangling DNS, And Hacks That Could Have Been Worse
The author of the BlueHammer exploit, which was released earlier this month and addressed in the last Patch Tuesday, continues to be annoyed with the responses from the Microsoft security research …

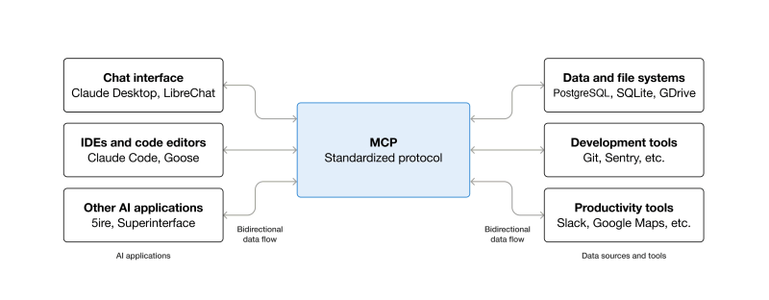
How Anthropic’s Model Context Protocol Allows For Easy Remote Execution
As part of the effort to push Large Language Model (LLM) ‘AI’ into more and more places, Anthropic’s Model Context Protocol (MCP) has been adopted as the standard to connect LLMs …

Encrypting Encrypted Traffic To Get Around VPN Bans
VPNs, Virtual Private Networks, aren’t just a good idea to keep your data secure: for millions of people living under restrictive regimes they’re the only way to ensure full access to t…

This Week In Security: Docker Auth, Windows Tools, And A Very Full Patch Tuesday
CVE-2026-34040 lets attackers bypass some Docker authentication plugins by allowing an empty request body. Present since 2024, this bug was caused by a previous fix to the auth workflow. In the 202…

This Week In Security: Docker Auth, Windows Tools, And A Very Full Patch Tuesday
CVE-2026-34040 lets attackers bypass some Docker authentication plugins by allowing an empty request body. Present since 2024, this bug was caused by a previous fix to the auth workflow. In the 202…