Malware hunting and new ReVa release demo live at https://twitch.tv/cyberkaida
One of the places where #AI has helped me out a lot is in the resurrection of abandoned projects in my graveyard of git repos that were "good enough" - but I had no time to work on.
@rick-gnous filed a defect on a 5-year-old UF2 loader I wrote because I wanted to spend time hacking on the #defcon29 #badge back in the day. Since then, UF2 has made multiple appearances and #Ghidra has been though many releases.
After burning some #gemini credits, there is now a nicer #UF2 loader for Ghidra, with tests and even tests that show the bug is fixed.
Should the the next @defcon (#DEFCON34) badge need it, you might want to take a look:
🔍 Abstracting The Hardware: Bridging Renode and Ghidra for Embedded Vulnerability Research with Open Source
Dawid Pietrykowski, inżynier oprogramowania w Antmicro, pokaże jak wykorzystać #Renode i #Ghidra do analizy firmware oraz badania bezpieczeństwa systemów wbudowanych — bez użycia fizycznego sprzętu.
📍 Gdzie? Wydział Matematyki i Informatyki UAM w Poznaniu
📅 Kiedy? 30.05.2026
👉 Sprawdź agendę: https://piwo.sh
🎟️ ODBIERZ BILET: https://app.evenea.pl/event/piwo2026/
https://github.com/NationalSecurityAgency/ghidra/blob/Ghidra_12.1_build/Ghidra/Configurations/Public_Release/src/global/docs/ChangeHistory.md
My first contribution (#6827) landed after *checks notes* 19 months :D
Ghidra-SNES: A Ghidra extensio...
Hey, this is a real joy to use. Thanks @clearbluejar !
I mean, not to complain _too_ loudly on Ghidra's UI but ... prompting really is a better UX here.

pyghidra-mcp Meets Ghidra GUI: Drive Project-Wide RE with Local AI
pyghidra-mcp v0.2.0 ships a GUI-backed mode that lets a local LLM drive a live Ghidra CodeBrowser at full project scope. Renames, plate comments, and cross-binary pivots land in real time, with every edit tagged in Ghidra’s undo history while the session is alive.
https://github.com/0xeb/libghidra
#Ghidra
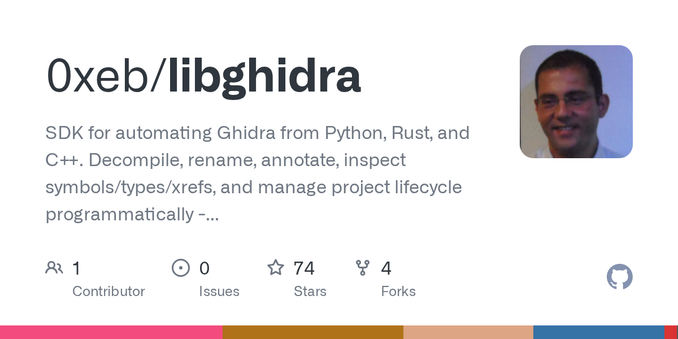
GitHub - 0xeb/libghidra: SDK for automating Ghidra from Python, Rust, and C++. Decompile, rename, annotate, inspect symbols/types/xrefs, and manage project lifecycle programmatically - treat Ghidra like infrastructure, not just a GUI.
SDK for automating Ghidra from Python, Rust, and C++. Decompile, rename, annotate, inspect symbols/types/xrefs, and manage project lifecycle programmatically - treat Ghidra like infrastructure, not...
My work's been done with #Ghidra, and I've written custom #Python tools to do it. Including a custom exporter for an annotated HTML disassembly (https://chipx86.com/faxanadu/), #Mesen labels files, and source code that can be compiled with the ca65 compiler.
I've open sourced all that today:
Реверс — это сканворд. Как я впервые нормально понял Ghidra
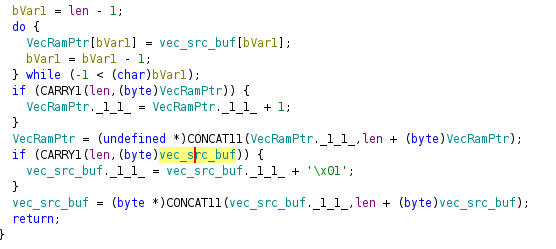
Привет, Хабр. У меня бывают неожиданные заказы, из неожиданных сфер на фрилансе. Недавно писал про то как прилетел большой проект по классификатору фоток. А теперь пришел запрос на реверс! Не могу вдаваться в подробности проекта - много конфиденциального - но я расскажу про конкретный разбор одного .dll файла. Открыл Ghidra, кликнул на функцию, включил декомпилятор - и передо мной встала стена. Не метафорическая стена. Прям реально стена! И вот пока я эту функцию ковырял, переименовывал переменные, ходил по ссылкам, открывал соседние функции, смотрел строки, в какой-то момент меня щёлкнуло. Это же сканворд.
https://habr.com/ru/articles/1029296/
#reverse_engineering #ghidra #реверсинжиниринг #binary_analysis #dll #decompilation #xrefs #static_analysis #reverse #binary_parsing