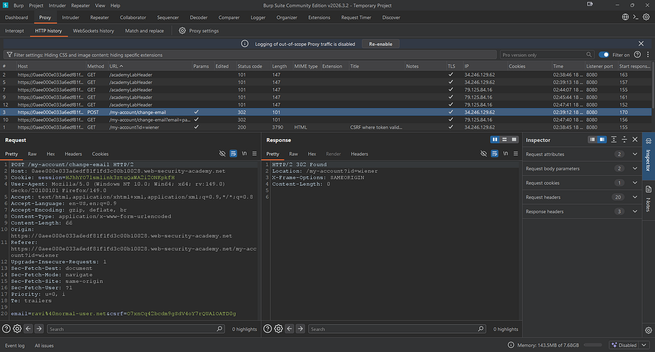
Day 5 — CSRF Token Bypass using GET Request
This article discusses a Cross-Site Request Forgery (CSRF) vulnerability where an attacker can bypass CSRF tokens by manipulating GET requests. The root cause is inconsistent validation of CSRF tokens across HTTP methods, particularly on GET requests. In this case, the application incorrectly validated CSRF tokens for GET requests but did so correctly for POST requests. By modifying a legitimate request to use the GET method and moving parameters into the URL, the researcher discovered that the server did not validate the CSRF token. The attack involves creating an HTML PoC (proof-of-concept) with JavaScript to automatically submit the modified request, exploiting the victim without their interaction. This vulnerability emphasizes the importance of consistent validation for CSRF tokens across all HTTP methods. Key lesson: Validate CSRF tokens consistently regardless of HTTP method to maintain security. #BugBounty #WebSecurity #CSRF #VulnerabilityResearch
https://smartpicks4u.medium.com/day-5-csrf-token-bypass-using-get-request-791cba29812d?source=rss