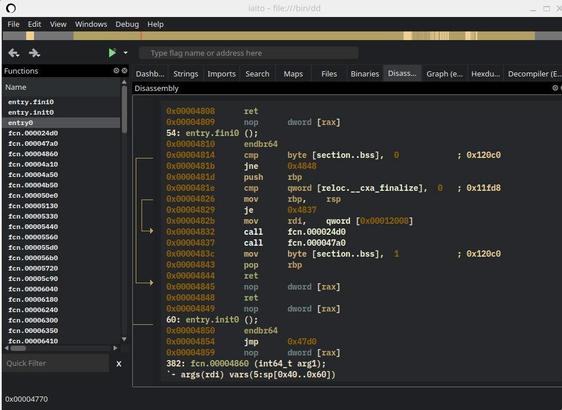
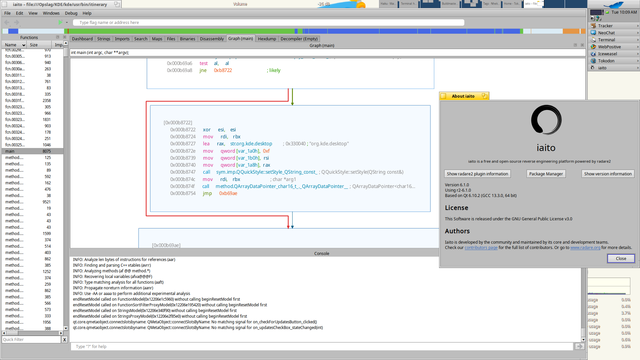
Iaito 6.1.4 is out! 💥
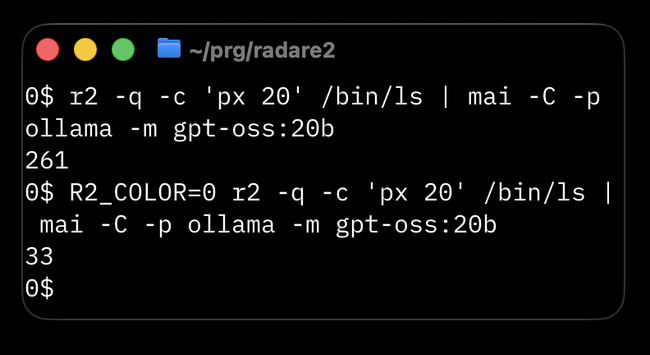
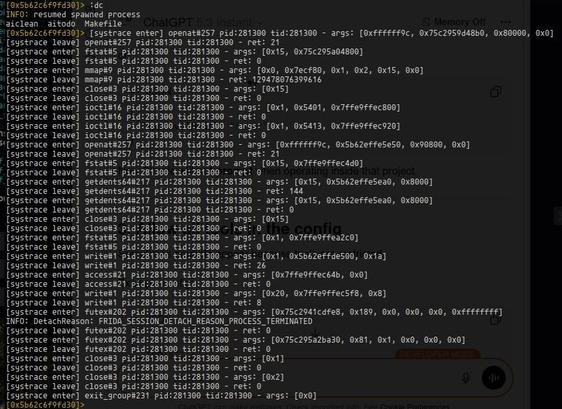
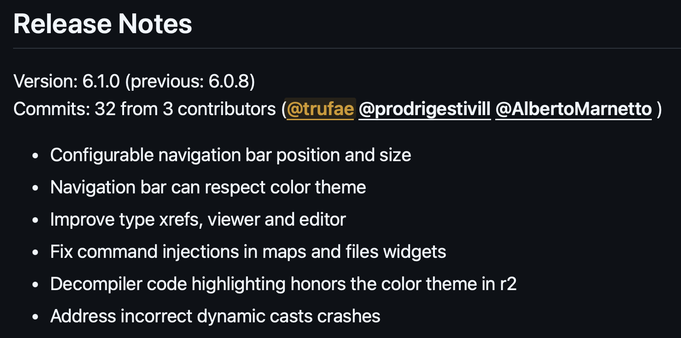
Tons of stability improvements, new widgets, userfriendly features, brings back the debugger mode, display analysis progress and background webserver ideal for r2mcp.
Full changelog https://github.com/radareorg/iaito/releases/tag/6.1.4 #reverseengineering
#radare2
 radare
radare