「どこにメモした?」をなくす無料の共有メモ帳 Dropbox Paperは家族旅行のプラン作りにも大活躍
https://ascii.jp/elem/000/004/402/4402632/?rss
Disclosing new PebbleDash-based tools
Kaspersky researchers conducted an in-depth analysis of Kimsuky APT activity, revealing tactical shifts and new malware variants based on the PebbleDash platform. The group introduced HelloDoor, a Rust-based backdoor, httpMalice leveraging HTTP and Dropbox communications, and updated MemLoad and httpTroy variants. Kimsuky maintains persistence through legitimate tools including VSCode Tunneling with GitHub authentication and DWAgent remote management software. Initial access occurs via spear-phishing with malicious attachments disguised as documents. The group primarily targets South Korean entities across government and defense sectors, with additional PebbleDash attacks observed in Brazil and Germany. Infrastructure relies on free South Korean hosting services and tunneling services like Cloudflare Quick Tunnels and Ngrok. Both PebbleDash and AppleSeed malware clusters demonstrate ongoing development with shared distribution methods, stolen certificates, and overlapping targets, indicating single-actor c...
Pulse ID: 6a05af0979e3cc1214a50d4e
Pulse Link: https://otx.alienvault.com/pulse/6a05af0979e3cc1214a50d4e
Pulse Author: AlienVault
Created: 2026-05-14 11:16:25
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#AppleSeed #BackDoor #Brazil #Cloud #CyberSecurity #Dropbox #Germany #GitHub #Government #HTTP #InfoSec #Kaspersky #Kimsuky #Korea #Malware #OTX #OpenThreatExchange #Phishing #RAT #Rust #SouthKorea #SpearPhishing #UK #bot #AlienVault
I have gone back to sharing zip files on my own server after decades of using other services, cos they are so enshittified and gated now.
The mere simple act of wanting to share music privately is impossible without some BS issue (people having to login, premium needed to share, etc).
Bandcamp - need premium to share private albums, Soundcloud others have to jump through hoops to login, etc.
I mean how do folks share demos and collab tracks nowadays? Dropbox? (same issue, you need to login etc).
I just want a free Soundcloud style player with a folder of tracks I can send the link privately to others without it needing to be public or others needing to login or pay!
Only one I've not checked recently but seemed to constantly want me to go premium/upgrade is Mediafire, maybe that still allows private share but doubtful it will remain to do that if it still does....
Flash Alert: EtherRat and TukTuk C2 End in The Gentleman Ransomware
An intrusion was observed in April 2026 where threat actors deployed EtherRAT malware through a malicious MSI installer disguised as a Sysinternals tool. The malware utilized Ethereum blockchain via EtherHiding for dynamic C2 configuration updates. Following reconnaissance activities, actors deployed TukTuk malware framework using DLL sideloading techniques with legitimate applications like Greenshot and SyncTrayzor. TukTuk established C2 channels through SaaS platforms including ClickHouse and Supabase, with backup channels via Ably, Dropbox, and GitHub Issues. The actors performed Kerberoasting, credential theft via Mimikatz and LSASS dumping, and deployed GoTo Resolve RMM tooling for lateral movement. Data exfiltration to Wasabi cloud storage was conducted using Rclone before deploying The Gentlemen ransomware domain-wide through a malicious GPO. The intrusion leveraged blockchain infrastructure, SaaS platforms, and decentralized services to evade traditional network defenses.
Pulse ID: 6a0200aec25a59a6b9d4edcf
Pulse Link: https://otx.alienvault.com/pulse/6a0200aec25a59a6b9d4edcf
Pulse Author: AlienVault
Created: 2026-05-11 16:15:42
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BlockChain #Cloud #CyberSecurity #Dropbox #EtherHiding #GitHub #InfoSec #Malware #OTX #OpenThreatExchange #RAT #RansomWare #Rclone #SideLoading #UK #bot #AlienVault
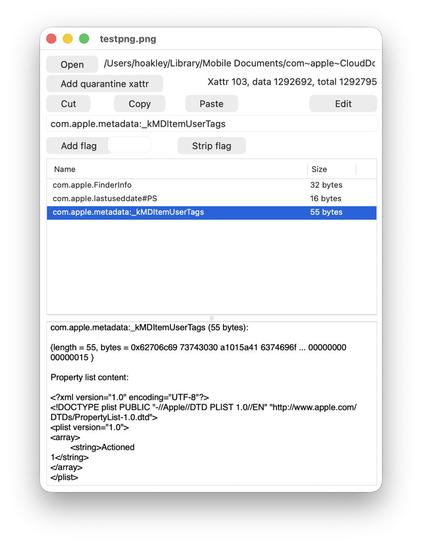
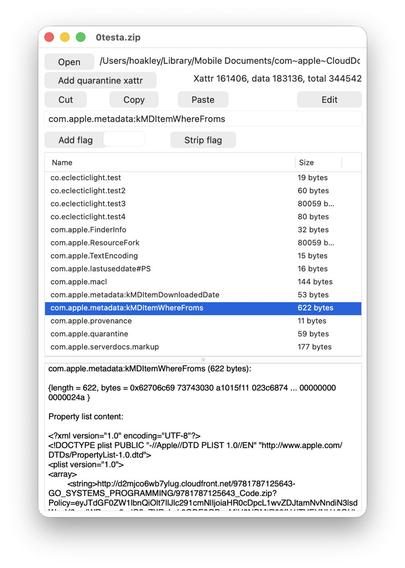
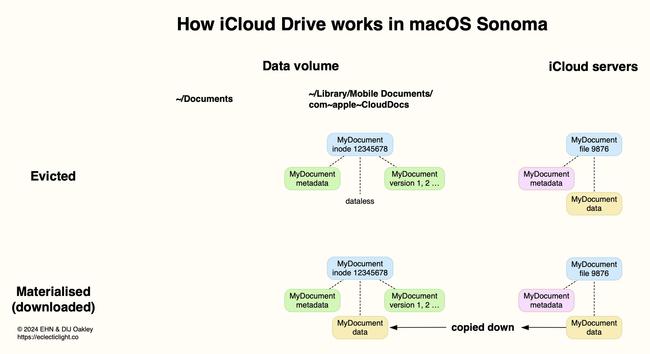
Does iCloud Drive now lose almost all metadata?
Explainer: File Provider and cloud services
Der neu entwickelte Cloud-Service Tuta Drive steht derzeit in der geschlossenen Beta-Phase und bietet Nutzern verschlüsselten Speicherplatz.
{ #Szene #Google #Datenschutz #Dropbox #Angriff }
>> https://nydus.org/news/135655-tuta-drive-ein-innovativer-ansatz-im-cloud-speicher-sektor.html
 ASCII.jp - トップ
ASCII.jp - トップ