Inotiv settles cybersecurity class action — here's what boards and executives should know.
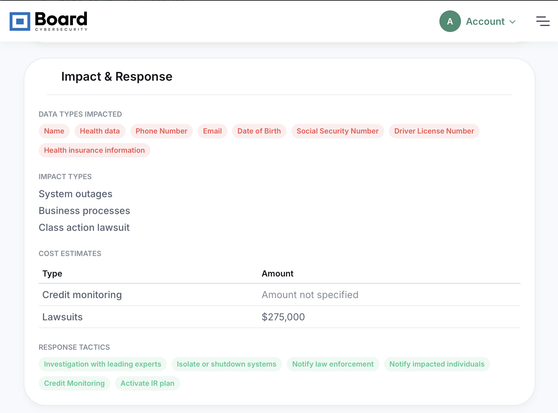
The company filed an 8-K today confirming a settlement agreement resolving litigation stemming from its August 2025 data breach. PHI and PII were among the data potentially acquired.
The settlement, if court-approved, provides class members with:
• Compensation for lost time and out-of-pocket expenses
• Recovery for extraordinary losses
• An alternative flat cash payment
• Two years of credit monitoring
Attorneys' fees are capped at $275,000. The company anticipates full insurance coverage for all settlement payments.
No admission of liability. Three federal cases were dismissed and refiled in Indiana state court before this resolution.
This is a useful case study in how post-breach litigation tends to consolidate and settle — and why cyber liability insurance structuring matters from day one.
Full incident profile: https://www.board-cybersecurity.com/incidents/tracker/inotiv-cybersecurity-incident-f965dc60?utm_source=mastodon&utm_medium=social&utm_campaign=inotiv-update
#CyberSecurity #DataBreach #BoardGovernance #CyberRisk #PrivacyLaw