Security is no longer optional — it’s critical.
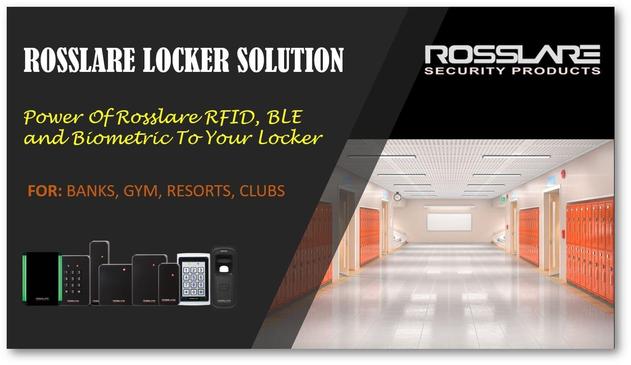
With Rosslare Access Control Systems, ensure only authorized access across your facility.
✔️ Smart Controllers
✔️ RFID & Biometric Integration
✔️ Centralized Monitoring
📞 Contact SARC Infosolution
📱 +91-9594283444
📧 [email protected]
📢 WhatsApp Channel: https://zurl.co/k3gHX
#AccessControl #Rosslare #SecuritySolutions #SmartSecurity #SARC #SARCInfosolution