Another talk announcement for BSides Luxembourg!
🔥🤖 𝗢𝗛 𝗦𝗛𝗜𝗧 𝗜 𝗔𝗖𝗖𝗜𝗗𝗘𝗡𝗧𝗔𝗟𝗟𝗬 𝗕𝗥𝗘𝗔𝗖𝗛𝗘𝗗 𝗔𝗡 𝗢𝗥𝗚𝗔𝗡𝗜𝗭𝗔𝗧𝗜𝗢𝗡 (𝗢𝗥 𝗠𝗔𝗡𝗬) 𝗨𝗦𝗜𝗡𝗚 𝗔𝗜 – Panagiotis Fiskilis 💥
What starts as a harmless search can spiral into a multi-organization data breach—especially when AI gets involved.
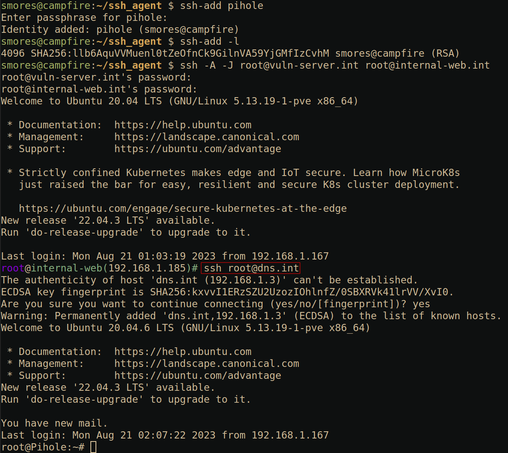
This talk dives into real-world research showing how AI can be weaponized for OSINT, enabling large-scale data discovery, spear phishing campaigns, and even manipulation of AI systems themselves. From injecting malicious context into models to scaling attacks via APIs and agent workflows, this session explores how adversaries can turn AI into a powerful offensive tool—and how defenders can detect and respond.
Expect a true purple team perspective, blending attacker techniques with defensive insights, including OPSEC considerations and strategies to identify malicious AI-driven activities before they escalate.
Panagiotis Fiskilis is a Senior Red Team Operator at NVISO, specializing in API hacking, Active Directory exploitation, and malware development. With multiple industry certifications (OSCP, OSWE, CRTO, eWPT and more), he brings hands-on offensive expertise combined with a strong research-driven mindset.
📅 Conference Dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule Link: https://pretalx.com/bsidesluxembourg-2026/schedule/
👉 Browse sessions, track talks in real time, and plan your schedule on Hacker Tracker: https://hackertracker.app/schedule?conf=BSIDESLUX2026
#BSidesLuxembourg2026 #AISecurity #RedTeam #OSINT #CyberSecurity #AI #ThreatIntelligence #PurpleTeam