Happy Monday folks, I hope you had a restful weekend and managed to take a breather from all things cyber! Time to get back into it though, so let me give you hand - catch up on the week’s infosec news with the latest issue of our newsletter:
https://opalsec.substack.com/p/soc-goulash-weekend-wrap-up-09e?sd=pf
#Emotet are back and are using…OneNote lures? ISO disk images? Malvertising? Nah – they’re sticking with tier tried and true TTPs – their Red Dawn maldoc template from last year; macro-enabled documents as lures, and null-byte padding to evade automated scanners.
We’ve highlighted a report on the Xenomorph #Android Banking Trojan, which added support for targeting accounts of over 400 banks; automated bypassing of MFA-protected app logins, and a Session Token stealer module. With capabilities like these becoming the norm, is it time to take a closer look at the threat Mobile Malware could pose to enterprise networks?
North Korean hackers have demonstrated yet again that they’re tracking and integrating the latest techniques, and investing in malware development. A recent campaign saw eight new pieces of malware distributed throughout the kill chain, leveraging #Microsoft #InTune to deliver payloads and an in-memory dropper to abuse the #BYOVD technique and evade EDR solutions.
A joint investigation by #Mandiant and #SonicWall has unearthed a two-year campaign by Chinese actors, enabled through exploitation of unpatched SMA100 appliances and delivery of tailored payloads. A critical vulnerability reported by #Fortinet this week helps reinforce the point that perimeter devices need to be patched with urgency, as it’s a well-documented target for Chinese-affiliated actors.
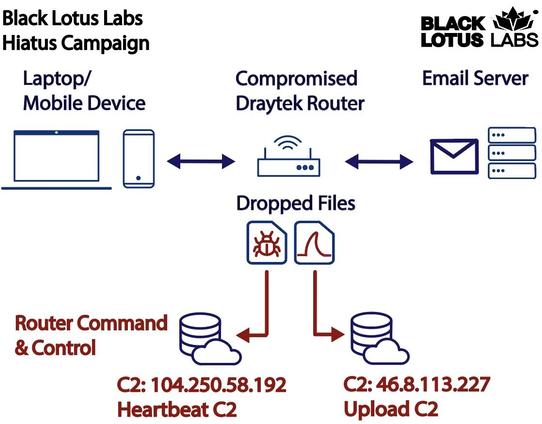
#HiatusRAT is a novel malware targeting #DrayTek routers, sniffing network traffic and proxying C2 traffic to forward-deployed implants. TTPs employed in recent #BatLoader and #Qakbot campaigns are also worth taking note of, as is #GoBruteforcer, a new malware family targeting specific web server applications to brute force logins and deploy an IRC bot for C2.
Those in Vulnerability Management should take particular note of the #Veeam vulnerability, which appears trivial to exploit and actually delivers plaintext credentials to the attacker. CISA have also taken note of nearly 40k exploit attempts of a 2 year old code-exec-as-root vulnerability in the #VMWare Cloud Foundation product in the last two months, so make sure you’re patched against it.
#Redteam members have some excellent reading to look forward to, looking at HTTP request smuggling to harvest AD credentials and persisting with a MitM Exchange server, as well as a detailed post that examines #CobaltStrike’s reflective loading capability;
The #blueteam has some great tradecraft tips from @inversecos on #Azure DFIR, as well as tools to help scan websites for malicious objects, and to combat the new #Stealc #infostealer and well-established Raccoon Stealer.
Catch all this and much more in this week's newsletter:
https://opalsec.substack.com/p/soc-goulash-weekend-wrap-up-09e?sd=pf
#infosec #cyber #news #cybernews #infosec #infosecnews #informationsecurity #cybersecurity #newsletter #hacking #security #technology #hacker #vulnerability #vulnerabilities #malware #ransomware #dfir #soc #threatintel #threatintelligence #DarkWeb #mdm #dprk #FortiOS #FortiProxy

 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉