You finally get a seat at the table, literally. You become a senior manager, or a director, or a VP. Now, you’re in the conference room, sitting at that table with a group of your peers for some regular weekly meeting.
Something feels off. You recognize an invisible wall, a barrier. You know that there are things you don't know about the culture, the relationships, the "way things work," and how change can be made to happen.
Here's one of the two-sided secrets of power that some people are brought up knowing, but that many people only experience from one side.
As a leader, you should be comfortable with expecting obedience. I chose my word carefully: you should expect obedience, not cooperation.
Have you experienced this kind of leader? They have some aura that radiates outward. They don’t say, “If it’s alright with you,” they just kindly and politely tell you what they want done. They know you’re going to do it, and you know you’re going to do it. They don’t ask your permission or approval. They’re not mean or demanding. They just tell you what they expect you to do, and on your side, you know you’re going to do it.
Obedience is how things get done. Obedience is required.
Cooperation is how the doer feels about the doing. Cooperation is desired.
Now, back to the conference table and that weekly meeting. You'll be asked to report on what got done. You won't be asked how the doers felt about the doing.
Your inner power, your inner confidence, in that hour at the table, comes from all that happened in the preceding week. And what happened in the preceding week is the direct result of your expectation of obedience.
Yes, be humble.
Yes, be grateful.
Yes, show appreciation.
Yes, reward the achievers.
Yes, grow and develop your team.
These things evoke cooperation from the good hires.
But always - always! - expect obedience.
You're the leader. In another week, you're going to be back at the table, and the person you report to will want to know what got done.
#CallMeIfYouNeedMe #FIFONetworks
#leadership #management
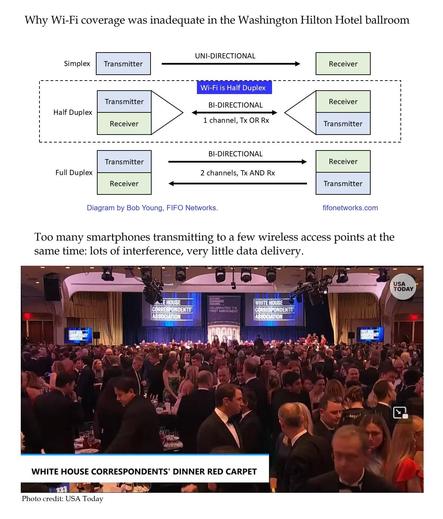
Cybersecurity - Networks - Wireless – Telecom – VoIP