🔍 Inside the Tech: New Talk Added to BSides Luxembourg
🌐📡 𝗧𝗛𝗘 𝗙𝗢𝗥𝗚𝗢𝗧𝗧𝗘𝗡 𝗙𝗜𝗡𝗚𝗘𝗥𝗣𝗥𝗜𝗡𝗧: 𝗗𝗡𝗦 𝗕𝗔𝗦𝗘𝗗 𝗢𝗦𝗜𝗡𝗧 𝗧𝗘𝗖𝗛𝗡𝗜𝗤𝗨𝗘𝗦 𝗙𝗢𝗥 𝗣𝗥𝗢𝗗𝗨𝗖𝗧 & 𝗦𝗘𝗥𝗩𝗜𝗖𝗘 𝗗𝗜𝗦𝗖𝗢𝗩𝗘𝗥𝗬 – Rishi ( @rxerium )
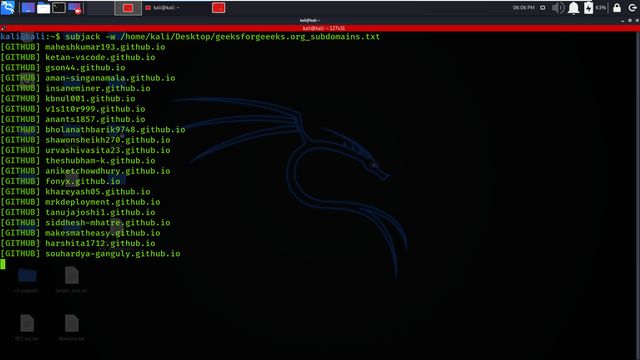
⚡ Reveal hidden infrastructure in a Talk (40 min) using DNS TXT records to map technologies, dependencies, and external services at scale.
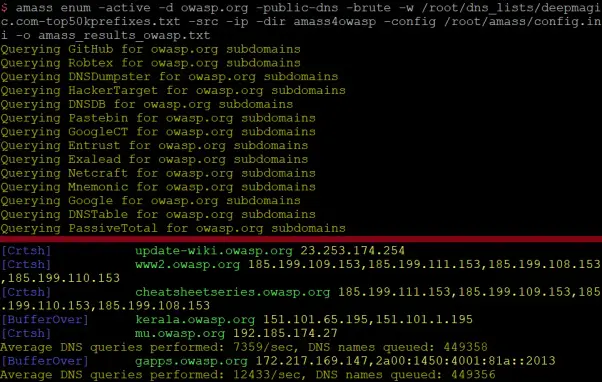
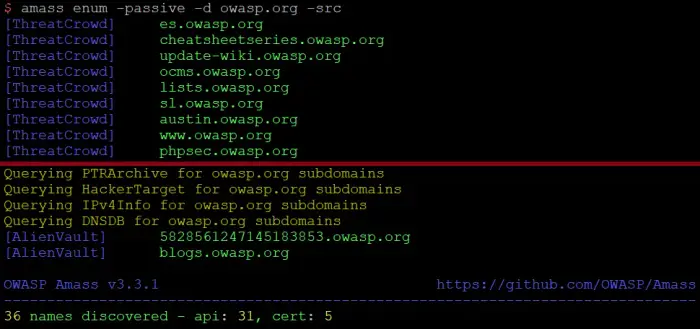
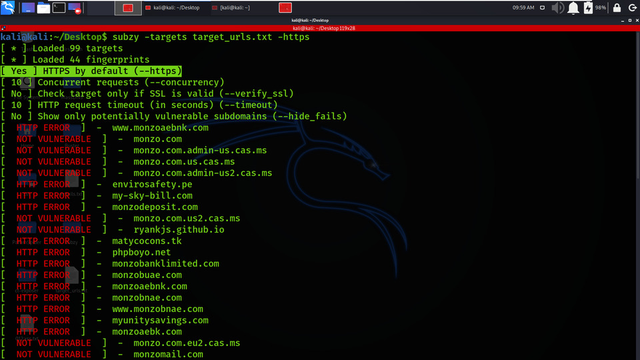
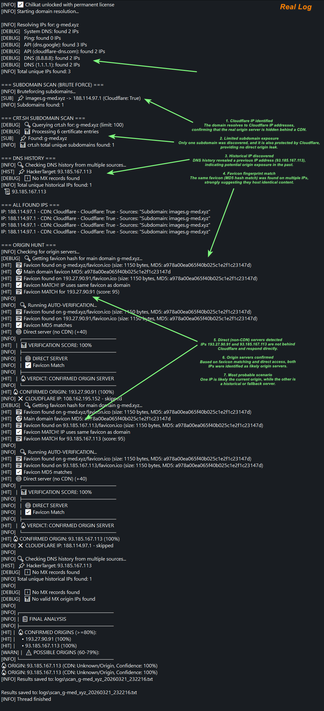
DNS is often treated as infrastructure plumbing, but TXT records quietly expose far more than most defenders realize. This session introduces a DNS-based OSINT methodology that leverages large-scale TXT record analysis to uncover embedded service dependencies such as cloud platforms, SaaS integrations, and identity providers.
By programmatically scanning DNS zones and integrating the technique into tools like Nuclei and OWASP Amass, this approach enables security teams to build detailed maps of organizational technology stacks and attack surfaces. A real-world case study from the Salesloft breach demonstrates how these signals translate into actionable intelligence for both offensive and defensive use cases.
Rishi ( @rxerium ) is a London-based security researcher focused on vulnerability research, threat intelligence, and OSINT-driven attack surface discovery. He contributes to open-source security tooling, supports the UK OSINT community, and focuses on building scalable reconnaissance and detection methodologies.
📅 Conference Dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule Link: https://pretalx.com/bsidesluxembourg-2026/schedule/
📲 View full schedule & build your agenda: https://hackertracker.app/schedule?conf=BSIDESLUX2026
#BSidesLuxembourg2026 #OSINT #DNS #AttackSurface #ThreatIntelligence #CyberSecurity