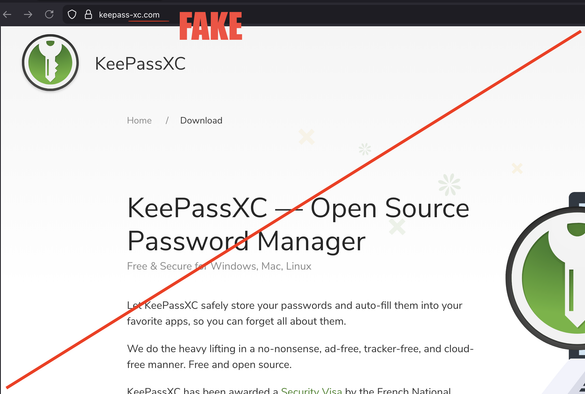
Methinks you should go buy as many typosquat domains as are available before copycats get to them.
@keepassxc @eroc1990
Yeah, that sounds like Whac-a-mole.
Anything else that can be done about it?
I just reported it to DuckDuckgo, it is the third result for "keepass xc" there currently -.-
Enter lots of fake emails to them? Possibly to domain that tarpits every access or something else that slows down them..
@keepassxc @eroc1990
I installed keepassxc yesterday in a hurry, normally I do pay a lot of attention to the URL, in hindsight not so sure...
So if I didn't have to enter an email, I should have chosen the right one? Or at least let's say, not this particular one?
Is the download malware that leaks the pw datatbase in plain text? Is the signature known to av programs?
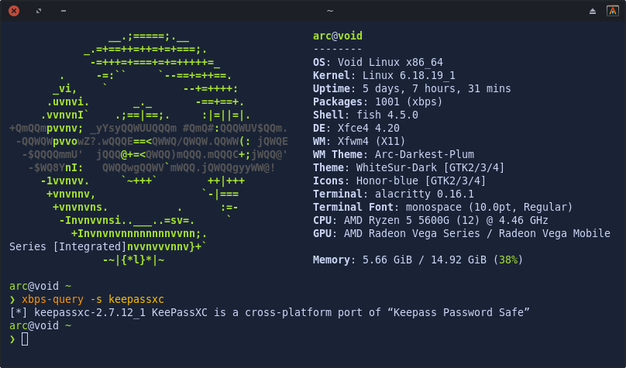
I guess you're using M$ Windows (otherwise you would have probably used a package manager).
If you still got the .MSI/.zip file, you can check the signature of the file like this:
https://keepassxc.org/verifying-signatures
(You can scroll all the way down for a simple hash sum check using PowerShell)
If it does match, your installer was legit :)
@keepassxc
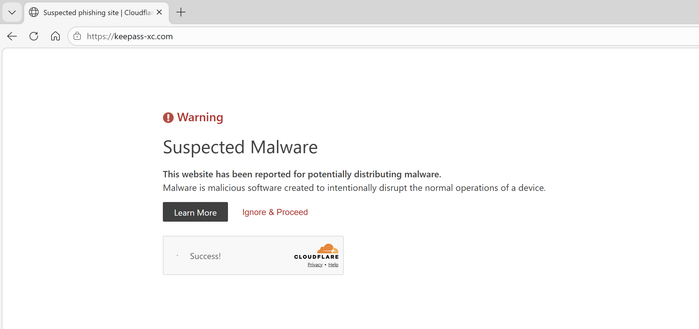
@keepassxc tango down.
CloudFlare shows suspected malware.
You need:
KeepassXC/com
KeepassXC/org
KeepassXC/net
maybe KeepassXC/pw as a "Joke Domain" and the same with "-". Since .com is currently taken it is one less.
I calculate now with 6 Domains, where we end up at around 70$ a year, if we add uncommon extensions or Country specific (in this Case I choose: .info, .biz and .eu) we are still at around 92$ a year. These are not even 1,2K$ a year. Idk what "weird" or uncommon Domains you own. But a basic Brand Shield with these should be enough. And sorry, I do not spend Money at Domain-Suckers/Re-Sellers, I sue the Shit out of them if they infringe my Brand.
@gremlin @keepassxc Why are you being so authoritative 😅? I get that you're trying to be helpful, but you're coming off very rude. Please be kind.
I agree with the Keepass admin that it probably isn't the best idea to spend all the donation funds on domains.
@wolfram_roesler @keepassxc You can't make up Boomer names like that, Wolfram; I donate enough to the FOSS community with my server performance, so don't worry about that.
But I'd love to return the favor. The KeepassXC team would be happy if you did, especially if you use their software. 😇
from repository
@keepassxc this reminds me to send a donation. Not to buy domains, but just because...
keepassxc is a fave.
@keepassxc
You can take over malicious domain quite easy.
Then you really should take your product to the typo-safe domain name ASAP. Possibly leveraging current publicity.
Always Check Your Sources! 5 mins of reasearch saves a lifetime of chasing down your own accounts!
We are on the same team. I'm reiterating your point. One "-" and because the user didn't check to be sure the link was right... all the hard work you guys put into these apps goes to immediate waste.
I apprciate this post from you helping users do that for your product.
Takedown completed.
If similar sites appear in the future, don’t hesitate to reach out! Always happy to support FOSS projects in protecting their users.
You can also easily report new cases here: https://justguard.be/report
Of course, there’s no full takedown until the domain is placed on client/server hold. That's correct!
That said, in practice, I rarely see any recovery once Cloudflare puts up a warning page. It’s usually easier for the threat actor to register a new domain.
The good news is that this domain has already propagated across most major AV vendors, and I’ve shared both the domain indicators and the associated malware samples with several partners and information-sharing networks (Quad9, GCA, GSE, etc.). That should help ensure any residual risk is blocked at multiple layers.
I'll set up some monitoring for both this domain and any future attempts to impersonate KeePassXC.
@jeroengui : I very much appreciate your work, but, as a bullet proof proxy service, #CloudflareIsEvil - they're complicit to cybercrime.
Cloudflare warns for malware/phishing for a specific *URL*, not the domain.
A minor change in the adds (or a forwarding site if that is what these scammers use) would bypass Cloudflare's crap measure.
I never saw a malware/phishing warning while opening:
https:⧸⧸keepass-xc.com/index.php
Note: I understand that blocking https:⧸⧸sites.google.com for a single malicious page would be problematic, but that's rather due to the fact that Google Sites sucks.
@ErikvanStraten @jeroengui They forwarded our abuse report to the hoster of the actual page. We’ll see.
Also everyone, if you must visit the page, at least do it in a private window or clear your history afterwards, so you don’t accidentally open it again later!