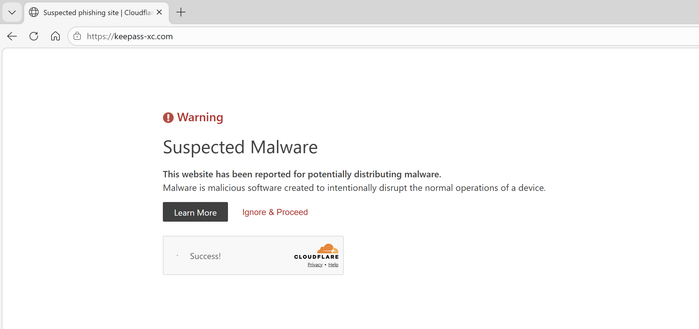
Takedown completed.
If similar sites appear in the future, don’t hesitate to reach out! Always happy to support FOSS projects in protecting their users.
You can also easily report new cases here: https://justguard.be/report
Of course, there’s no full takedown until the domain is placed on client/server hold. That's correct!
That said, in practice, I rarely see any recovery once Cloudflare puts up a warning page. It’s usually easier for the threat actor to register a new domain.
The good news is that this domain has already propagated across most major AV vendors, and I’ve shared both the domain indicators and the associated malware samples with several partners and information-sharing networks (Quad9, GCA, GSE, etc.). That should help ensure any residual risk is blocked at multiple layers.
I'll set up some monitoring for both this domain and any future attempts to impersonate KeePassXC.
@jeroengui : I very much appreciate your work, but, as a bullet proof proxy service, #CloudflareIsEvil - they're complicit to cybercrime.
Cloudflare warns for malware/phishing for a specific *URL*, not the domain.
A minor change in the adds (or a forwarding site if that is what these scammers use) would bypass Cloudflare's crap measure.
I never saw a malware/phishing warning while opening:
https:⧸⧸keepass-xc.com/index.php
Note: I understand that blocking https:⧸⧸sites.google.com for a single malicious page would be problematic, but that's rather due to the fact that Google Sites sucks.
@ErikvanStraten @jeroengui They forwarded our abuse report to the hoster of the actual page. We’ll see.
Also everyone, if you must visit the page, at least do it in a private window or clear your history afterwards, so you don’t accidentally open it again later!