Some are misreading the 2026 DBIR, skimming the headlines, but missing the bigger picture.
4 Takeaways:
1) Credentials appear in 39% of breaches across the full attack chain
2) Detection stacks often fire on auth events, but attackers have moved post-auth.
3) 3rd-party identity risk up 60% YoY
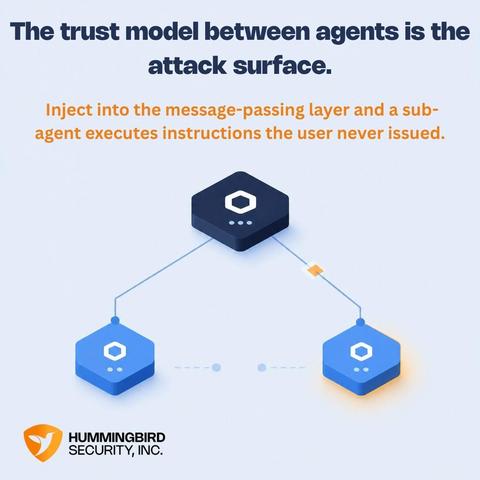
4) AI agents flagged as the next target. Vulns get them in. Identity is how they move.
We can help.