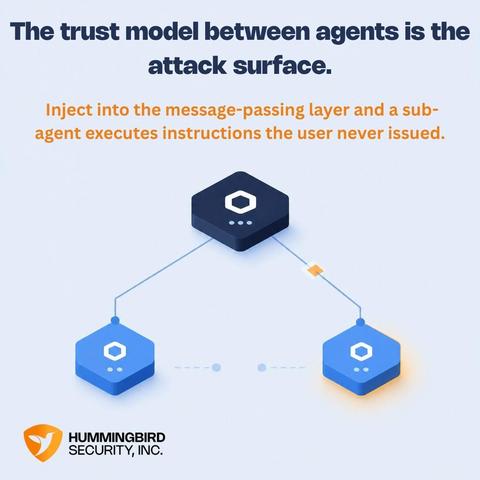
The AI agent security conversation focuses on individual agents.
The more interesting threat is one layer up at the communication layer between agents.
Inject into the message-passing layer, and a sub-agent executes instructions the orchestrator never issued. Valid credentials. Authorized calls. No obvious anomaly.
The agent that appears responsible may be entirely innocent - used as a relay.
That's the detection frontier. We can help.
gethumming.io
#ITDR #IVIP #IdentitySecurity #AIAgents