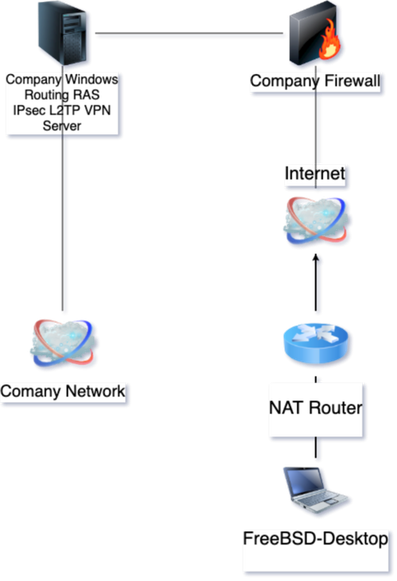
FreeBSD als IPsec/L2TP-Client für Microsoft Windows Routing und RAS VPN
FreeBSD 12 als IPsec/L2TP-Client gegen Windows RRAS konfiguriert: strongSwan + mpd5, IKEv1, 3DES-SHA1, MS-CHAPv2-Auth, MPPE-Encryption. Manuelle Route-Verwaltung. Windows-Enterprise-VPN erfordert Spezialwissen, aber machbar.
How To Set Up An IPsec With IKEv2 VPN Server On An Ubuntu Linux Cloud Server (VPS)
A 15-year-old flaw in strongSwan lets attackers crash VPNs using a simple integer underflow flaw. No auth needed, affects versions used for over a decade. Patch now.
Read: https://hackread.com/strongswan-flaw-attackers-crash-vpn-integer-underflow/
CVE Alert: CVE-2026-25075 - strongSwan - strongSwan - https://www.redpacketsecurity.com/cve-alert-cve-2026-25075-strongswan-strongswan/
#OSINT #ThreatIntel #CyberSecurity #cve-2026-25075 #strongswan #
#TIL Fortinet IPsec VPNs: they claim to support IKEv2 2FA (Certificate + EAP password), but they don't strictly enforce RFC 4739 for multiple authentication rounds.
If a native client (like strongSwan) ignores the cert and just asks for EAP, the FortiGate silently accepts it and falls back to password-only. It literally fails open!
If you are using #StrongSwan on your #Proxmox hypervisors: look out for https://github.com/strongswan/strongswan/discussions/2906
[solved] charon-systemd gets terminated by systemd under Debian 13 with Proxmox kernel 6.14.11-3-pve · strongswan strongswan · Discussion #2906
This is probably more of a kernel problem caused by changes made by the Proxmox team to the kernel. I am asking for some guidance to diagnosing this so I can write a proper bug report against Proxm...
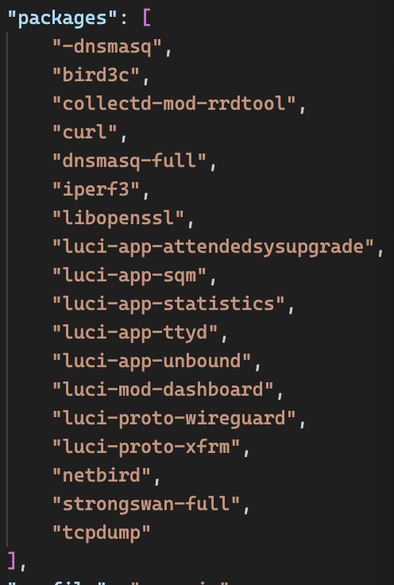
Anything missing for a general purpose x86 router?
#StrongSwan for my reverse proxy setup, and #netbird eventually for future usage.
Wow! After delving into IPSec strongSwan rekeying, I now know that the initial 'data key' (Child SA) is like a quick handshake with no fancy secret exchange (PFS) (RTFM! [1]). However, for rekeys, it's full secret agent handshake mode! Writing the GitHub bug report, which turned out not to be a bug, helped me to understand my situation better. [2] Finally migrated to the new IPSEC connection setup in OPNsense and updated my blog post. [3]
(Now I expect to get answers, aka 'Use WireGuard!')
[1]: https://docs.strongswan.org/docs/latest/config/rekeying.html#_ikev2
[2]: https://github.com/opnsense/core/issues/8631
[3]: https://du.nkel.dev/blog/2021-11-19_pfsense_opnsense_ipsec_cgnat/
Настраиваем собственный IKEv2/IPSec VPN сервер с помощью StrongSwan.
https://dalek.zone/videos/watch/d85f7c47-0050-42f3-9da8-e3f82f54dc44