There are two updates from Broadcom for critical vulnerabilities: https://support.broadcom.com/web/ecx/security-advisory
- Mainframe Application Tuner 12.0.04 Vulnerability in REST API and GUI and a vulnerability in the OM Spool Web Interface
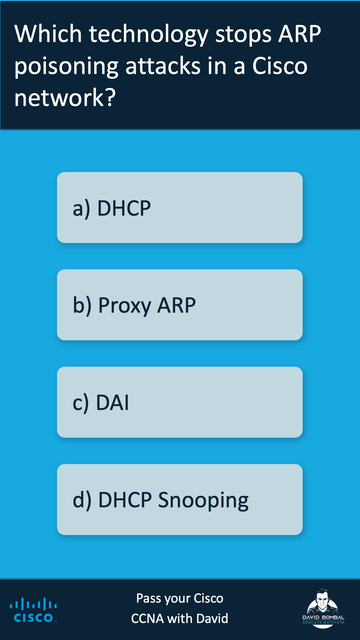
Cisco has three, one of them critical:
CRITICAL: CVE-2026-20230: Cisco Unified Communications Manager Server-Side Request Forgery Vulnerability https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-cucm-ssrf-cXPnHcW
MEDIUM: CVE-2026-20233: Cisco Webex Meetings Cross-Site Scripting Vulnerability https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-webex-xss-jw3NeQzS
MEDIUM: CVE-2026-20175: Cisco Finesse Remote File Inclusion Vulnerability https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-finesse-rfi-gwpkdc89 @TalosSecurity #infosec #Broadcom #vulnerability #Cisco