Wegen #Enkeltrick, auf den #Klöckner und Co reingefallen sind.
Klar kann man da hochnäsig behaupten, das würde einem selbst nicht passieren, aber #SocialHacking ist ein Ding. Bei etwas klügeren Ansätzen seid ihr auch dran.
I've been trying to delete an account for months. The company is completely stubborn and requires me to scan my ID and send it by email (yeah, right) so they can verify my date of birth.
Last night, I had an idea. Social engineering deluxe: I simply replied to the ticket email: ‘Thank you for confirming my date of birth. Do you need anything else? Can you now proceed with deleting the account?’
And the reply: ‘Your account has been marked for deletion.’
WIN!
Rachel Tobac é especialista em engenharia social. Mantém a empresa Social Proof Security, que ajuda a identificar falhas na segurança de empresas e ensina como melhorar os procedimentos de verificação de identidade.
Be politely paranoid
Rachel Tobac (1h09 no vídeo no final desse post)
O vídeo ao final tem 1h10 e vale a pena porque é bem divertido! Vou destacar os prontos principais, […]
#HACKING si ya kwenye #kompyuta tu ...BUT pamoja na kuchezea akili ya mtu ifanye jinsi unataka kuliko jinsi mwenye hiyo akili anataka afanye. AU?
#socialhacks #socialhacking #hackingtips #5021tips #hackers #howtohack #HapaUjanjaTu #mindhacks #mindhacking #socialengineering #socialhacker
.
.
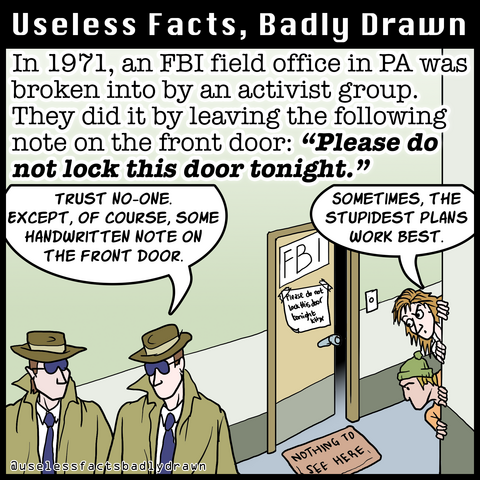
#mediapa #fbi #socialhacking #pennsylvania #spying #hacking #espionage #cointelpro #counterintelligence #history #funfacts #facts #webcomic #comics #uselessfacts #uselessfactsbadlydrawn
@q Which reminds me how fucked up and fundamentally broken #SSL is and that the entire #RentSeeking businesses of #CA's must be abolished.
Instead of @letsencrypt, we should've pushed for #CAcert since the latter one actually does #DueDiligence and is harder to penetrate or even abuse than getting an EV-SSL - cert fraudulently via #SocialHacking...