Why Predictability Increases Risk in the West Philippine Sea
By Cliff Potts, CSO, and Editor-in-Chief of WPS News
Baybay City, Leyte, Philippines — April 14, 2026
The Problem: Repetition Creates Opportunity
Maritime operations become easier to disrupt when they follow predictable patterns.
Fixed resupply dates, repeated routes, and consistent timing allow interfering vessels to plan ahead. Once patterns are identified, positioning assets becomes simpler. Interference shifts from reactive to pre-positioned.
This reduces effort. It also increases success rates.
Predictability turns routine operations into scheduled targets.
How Pattern Recognition Works in Practice
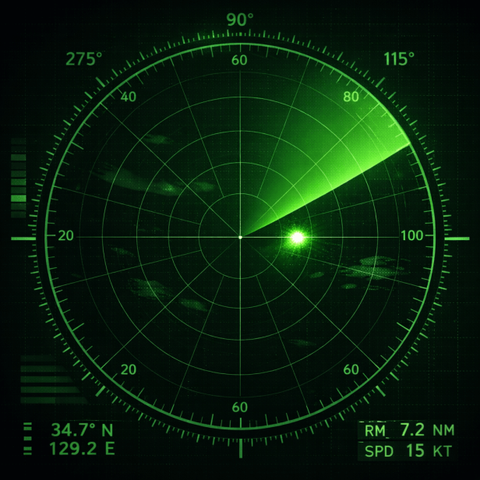
Maritime environments are observable.
Vessel movements can be tracked through radar, visual observation, and automatic identification systems. Even without complete data, repeated behavior creates patterns that can be inferred.
If a resupply mission departs at similar times each month and follows the same route, it can be anticipated. If patrols operate on fixed cycles, gaps can be identified.
Interference relies on this predictability.
Why Variation Disrupts Interference
Variation forces uncertainty.
When departure times shift, routes change, and mission durations vary, interference becomes harder to coordinate. Assets must remain on station longer. Coverage must expand. Timing becomes less reliable.
This increases cost and reduces efficiency.
Variation does not eliminate interference. It reduces its precision.
Controlled Unpredictability as a Method
Effective variation is structured, not random.
Operations should:
- Vary departure times within defined windows
- Alternate routes where possible
- Adjust mission sequencing
- Use staggered movements instead of single departures
The goal is not confusion within Philippine operations. The goal is uncertainty for observers.
Controlled unpredictability maintains coordination while reducing exposure.
Interaction With Routine Presence
Variation does not replace routine presence.
Routine presence establishes continuity. Variation alters the details within that continuity. Together, they create a system that is active but not easily predicted.
This balance is critical. Pure unpredictability creates internal risk. Pure routine creates external vulnerability.
Documentation Under Variable Conditions
Variation must not degrade documentation.
Standard recording procedures must remain consistent even as operations change. Time, location, and behavior data must still be captured accurately.
Changing patterns should not result in incomplete records.
Limits and Constraints
Not all operations can vary freely.
Geography, weather, and equipment limitations restrict options. Some routes are fixed by necessity. Some schedules are tied to operational requirements.
Variation should be applied where it reduces risk without compromising mission success.
Bottom Line
In the West Philippine Sea, predictable operations are easier to disrupt. Variation introduces uncertainty that increases the cost of interference.
By adjusting timing, routes, and sequencing within a controlled framework, the Philippines can reduce vulnerability without escalation. The objective is not randomness. The objective is to remain effective while becoming harder to predict.
For more social commentary, please see Occupy 2.5 at https://Occupy25.com
References (APA)
Bateman, S. (2017). Maritime security and law enforcement in the South China Sea. Contemporary Southeast Asia, 39(2), 221–245.
Erickson, A. S., & Kennedy, C. (2016). China’s maritime militia. Center for Naval Analyses.
Permanent Court of Arbitration. (2016). The South China Sea Arbitration (Philippines v. China).
United Nations. (1982). United Nations Convention on the Law of the Sea.
#grayZoneConflict #maritimeOperations #MaritimeSecurity #operationalSecurity #PhilippineCoastGuard #southChinaSea #UNCLOS #WestPhilippineSea