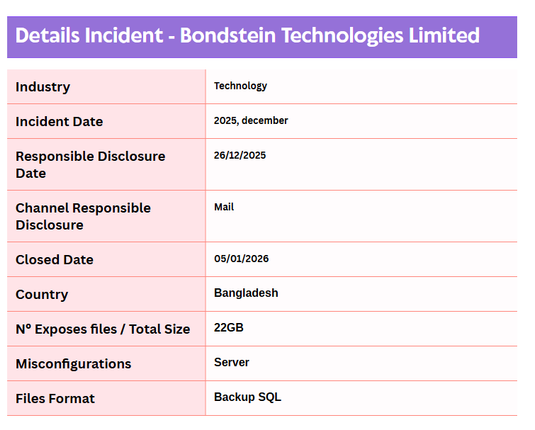
🇧🇩 Today I'm going to talk about Bondstein Technologies Limited, a company based in Dhaka, Bangladesh. One of their servers was found to be completely open and unprotected.
Bondstein Technologies Limited is a Dhaka-based technology company specializing in Internet of Things (IoT) solutions and frontier technologies. Founded in 2014, it has established itself as a leading player in Bangladesh for vehicle tracking, industrial automation, and smart connectivity.
What data was exposed?
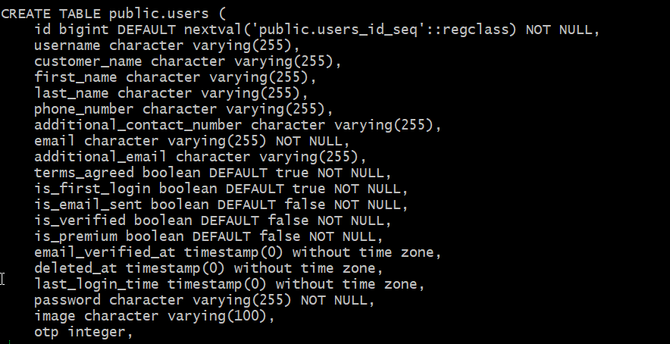
On December 26, 2025, I discovered that the server was exposing a 22 GB SQL backup file. According to the file timestamps and metadata, this backup appears to have been publicly accessible since at least July 2025.Among the files in the backup was users.sql, which contained the following sensitive fields:
username, customer_name, First_name, Last_name, Phone_number, Additional_contact-number, email, password.
*I was able to confirm that some of the employee names were real.
Additional findings:
The exposed server's IP resolved to a properly certified HTTPS server using a subdomain under .bondstein.net. The same IP also hosted a login portal (which I did not attempt to access).With this information, we were able to accurately identify the owner and submit a responsible disclosure.
Notification:
All of this was detailed in the email I sent to several Bondstein employees on December 26, 2025. When I checked again on January 5, 2026, the exposure had been fully closed. I followed up via email to inquire about any possible reward. On January 6, they replied with the following message:
Hi Chum1ng0,
Thank you for your responsible and detailed disclosure regarding the open directory issue on our server. We sincerely appreciate you taking the time and effort to notify us of this vulnerability, which allowed us to address it quickly. Your commitment to ethical research is truly valued. We want to confirm that the issue has been fixed and access has been restricted. We would also like to clarify that the server you identified is a staging server kept for internal purposes, and not a production environment. Regarding your request for a reward, we currently do not have an official bug bounty program in place. However, we are grateful for your help in securing our infrastructure.
We appreciate your patience and look forward to potentially collaborating in the future should we establish a formal program.
Sincerely
Bondstein
-NOT REWARD-
#VDP #responsibleDisclosure #misconfigurations #Bangladesh #cybersecurity #bondstein