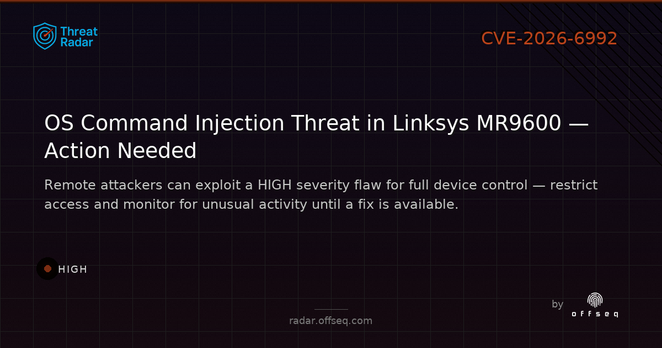
CVE Alert: CVE-2026-6992 - Linksys - MR9600 - https://www.redpacketsecurity.com/cve-alert-cve-2026-6992-linksys-mr9600/
#OSINT #ThreatIntel #CyberSecurity #cve-2026-6992 #linksys #mr9600
CVE Alert: CVE-2026-4558 - Linksys - MR9600 - https://www.redpacketsecurity.com/cve-alert-cve-2026-4558-linksys-mr9600/
#OSINT #ThreatIntel #CyberSecurity #cve-2026-4558 #linksys #mr9600
@web_martin @fds2610 Es gibt keinen offiziellen Weg von #Amazon. Jetzt hat jemand einen #Exploit entwickelt, der den Bootloader entsperrt und den Weg für CustomROMs freimacht.
#LineageOS bietet sich an, da es #OpenSource ist und für den Betrieb auf unterschiedlichster Hardware vorbereitet ist.
So ähnlich läuft es schon seit Jahrzehnten. #DBox2, #Linksys #WRT54G, Windows Mobile PDAs,... bei allen wurde die #Firmware reversed und dann wurden Alternativen entwickelt.
Teilweise sind aus diesen Entwicklungen neue Produkte, Firmen oder Communities entstanden.
DBox2->#Dreambox->div. #Linux Receiver
Linksys WRT54G->#OpenWRT/#DD-WRT->z.B. Gli.NET
Ob man diesen anfänglichen Versuchen vertraut, bleibt natürlich jedem selbst überlassen. Ich find's jedenfalls super. Endlich geht sowas mal wieder 😀
It would be interesting to hear the original justification for adding the following to the #Linksys MX4200 iptables:
-A INPUT -i eth0 -j wan2self
-A wan2self -j wan2self_ports
-A wan2self_ports -p tcp -m tcp --sport 5222 -j xlog_accept_wan2self
-A xlog_accept_wan2self -j ACCEPT
It's not often you see something that is so difficult to argue to be something else than a deliberate #backdoor. https://seclists.org/fulldisclosure/2026/Feb/19
Bring out yer path traversal memes!!
Plethore of critical #Linksys MX4200 Wi-Fi router vulnerabilities (that were originally reported to Linksys nearly a year ago!) are still unfixed:
- [SYSS-2025-001] Linksys MX9600/MX4200 - Path Traversal https://seclists.org/fulldisclosure/2026/Feb/10
- [SYSS-2025-002] Linksys MX9600/MX4200 - Missing Authentication for Critical Function https://seclists.org/fulldisclosure/2026/Feb/11
- [SYSS-2025-009] Linksys MX9600/MX4200 - SQL Injection https://seclists.org/fulldisclosure/2026/Feb/12
- [SYSS-2025-010] Linksys MX9600/MX4200 - OS Command Injection https://seclists.org/fulldisclosure/2026/Feb/13
- [SYSS-2025-011] Linksys MX9600/MX4200 - OS Command Injection https://seclists.org/fulldisclosure/2026/Feb/18
- [SYSS-2025-014] Linksys MX4200 - Improper Verification of Source of a Communication Channel
https://seclists.org/fulldisclosure/2026/Feb/19
On first read it might appear that many of these vulnerabilities would only be exploitable by accessing the device non-WAN interface(s) from inside the local network. However, due to the SYSS-2025-014 vulnerability the normally "LAN only RCE" vulnerabilities (SYSS-2025-010 and -011) and SQL injection (SYSS-2025-009) can be performed from the WAN interface (read: the internet). The attacker merely needs to make the connection originate from port 5222 (which is trivial to arrange via local bind before connect).
Update: Users of Linksys MX4200 should upgrade to firmware version 2.0.7.216620 or later. While not all of the security issues are fixed, it at least should stop the attacks via the WAN interface (SYSS-2025-014). https://support.linksys.com/kb/article/952-en/
#linksys #fulldisclosure #vulnerability #infosec #cybersecurity
Thought I'd "simply" set up some #vlan: one main, one #IoT, and one for my #poe ip cameras.
It took some work to set it up on my #GL.iNET #Flint3 #router, my
#Linksys #LGS528P was simple to setup
But after some tweaking (8 hours later) it seems all is now going well.
Even @homeassistant works in the new setup