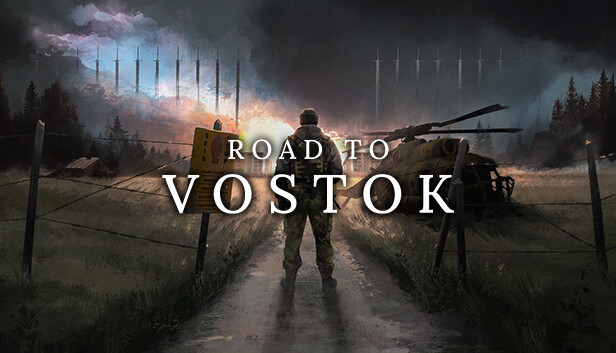
Road to Vostok is so accurate in locale and setting, it's uncanny. I grew up in a town next door, and did my military service in Hamina (many, many moons ago). https://store.steampowered.com/app/1963610/Road_to_Vostok/
| PGP | https://sintonen.fi/pgpkey.txt |
| Research | https://sintonen.fi/advisories/ |
| Github | https://github.com/piru |