Consistency and Coordination Patterns in Event-Driven Architecture
Consistency and Coordination Patterns in Event-Driven Architecture
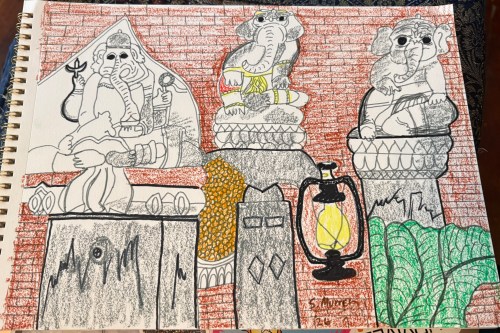
Building boundaries so we don’t absorb too much, especially for empaths; plus radio shows and sketches
Empaths are sponges and until we learn that we can either build boundaries to not absorb what we don't want, yet, OR we come to know that EVERYTHING works FOR our good, either to grow us or glow us like a slow burn candle… well then, we may FEEL too much (too much emotions), or react inappropriately and turn others off. And when we turn others off, it may take us YEARS (if ever), to reestablish those relationships--whether friend or family, such as when adult children cut off their parents […]https://nationalsecurityjournal.org/iran-destroyed-42-u-s-military-aircraft-in-operation-epic-fury-lessons-must-be-learned/ #Iran #Epic #Fury #USPlanes #ScrapMetal #LessonsLearned #GlobalReaction #HackerNews #ngated

Iran Destroyed 42 U.S. Military Aircraft in Operation Epic Fury: Lessons Must Be Learned
Iran destroyed 42 U.S. military aircraft in Operation Epic Fury — including 24 MQ-9 Reapers, 7 KC-135 Stratotankers, and 4 F-15E Strike Eagles. Drones swarmed Barksdale Air Force Base in waves of 12-15 for a week. 90% of Iran's underground missile storage facilities are still active.
Novice #DM here trying to run my first #ttrpg game without a module.
It's so darn easy to accidentally railroad your players.
They tell you to avoid it in all the tutorial videos, and you think of course you wouldn't do that.
What they don't tell you is in the heat of the moment you're thinking "I'll railroad my players to go here!!", instead you're thinking "oh, they misunderstood.. those NPCs aren't hostile, I'll just bring them over so they know ... " #lessonslearned
...However, her will was unbroken and she faced it alone, dying in the process. This triggered the closest Sacresants squad who had been finishing a second Carnifex and rushing to her aid. Aurelia's body could be retrieved with the remaining Rhino, but the crucial supplies on the planet were mostly lost.
- #OnePageRules altering activations are awesome!
- Paragons suck in OPR
- Sacresants are murderers in OPR
2/2
Some improv and mindfulness lessons from a five-day improv and mindfulness workshop I attended in Maine in 2016.
Check out the latest Indivisible Charlotte [PODCAST] “Operation Charlotte's Web: Community Leaders on the 2025 Immigration Enforcement Surge”
On Substack: https://indivisibleclt.substack.com/p/operation-charlottes-web-community
On YouTube: https://www.youtube.com/watch?v=qkvkQzyycyQ
On Facebook: https://www.facebook.com/share/v/1CiugEjHgh/
#ResistAndHeal #immigration #HealOurCulture #ICE #CBP #LessonsLearned #history #Charlotte