Smart Contracts for C&C: How ClearFake Hid in Plain Sight on BSC Testnet
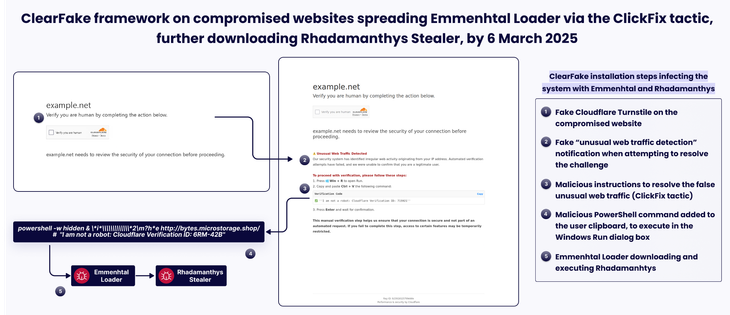
Threat actors exploited the EtherHiding technique to store ClearFake payload routing instructions within smart contracts on the BNB Smart Chain testnet, creating an immutable command-and-control infrastructure that cannot be taken down. The attack began with injected JavaScript on a compromised Swiss website that queried blockchain contracts to deliver malicious payloads. Victims passing anti-analysis checks were fingerprinted by operating system and routed to platform-specific ClickFix social engineering overlays. The campaign simultaneously deployed SectopRAT, a .NET-based remote access trojan capable of browser session hijacking, and ACRStealer, a C++ infostealer targeting credentials and cryptocurrency wallets. An on-chain execution tracker confirmed each compromise in real time. Four smart contracts shared a single deployer wallet, with the oldest deployed nearly a year before analysis, indicating a long-running, actively maintained operation.
Pulse ID: 6a15ba2632bd7e246e9c1250
Pulse Link: https://otx.alienvault.com/pulse/6a15ba2632bd7e246e9c1250
Pulse Author: AlienVault
Created: 2026-05-26 15:20:06
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BlockChain #Browser #CandC #ClearFake #CyberSecurity #EtherHiding #InfoSec #InfoStealer #Java #JavaScript #NET #OTX #OpenThreatExchange #RAT #RemoteAccessTrojan #SocialEngineering #Trojan #bot #cryptocurrency #AlienVault