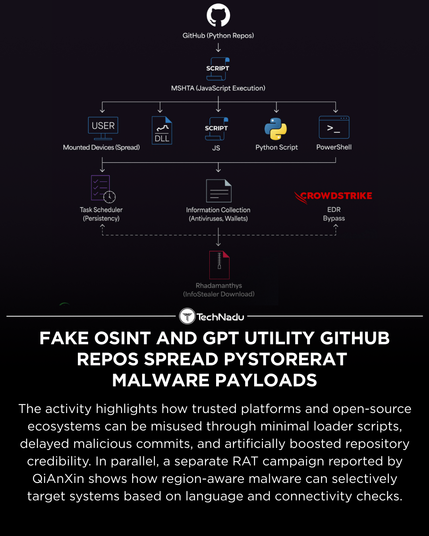
Researchers have documented a campaign abusing GitHub repositories themed as OSINT tools, GPT utilities, and developer resources to deliver PyStoreRAT, a modular, multi-stage remote access trojan.
The operation leverages delayed malicious commits, minimal loader stubs, reputation manipulation, and HTA-based execution to reduce early detection. In parallel, a separate RAT campaign demonstrates region- and language-aware targeting logic.
These cases underscore evolving tradecraft around trust abuse and script-based implants.
How are you adapting repository vetting and execution controls in your environment?
Source: https://thehackernews.com/2025/12/fake-osint-and-gpt-utility-github-repos.html
Engage in the discussion and follow TechNadu for measured infosec reporting.
#InfoSec #ThreatIntel #MalwareAnalysis #GitHubSecurity #OpenSourceRisk #TechNadu