GitHub links a repo breach to the TanStack npm supply-chain attack - one compromised dependency can ripple across thousands of developers. Trust in code must be continuously verified. 📦⚠️ #SupplyChainSecurity #OpenSourceRisk
Claude code leaked via malicious npm packaging - the supply chain remains a soft target for high-impact breaches. Trust in dependencies must be continuously verified. 📦⚠️ #SupplyChainSecurity #OpenSourceRisk
https://thehackernews.com/2026/04/claude-code-tleaked-via-npm-packaging.html
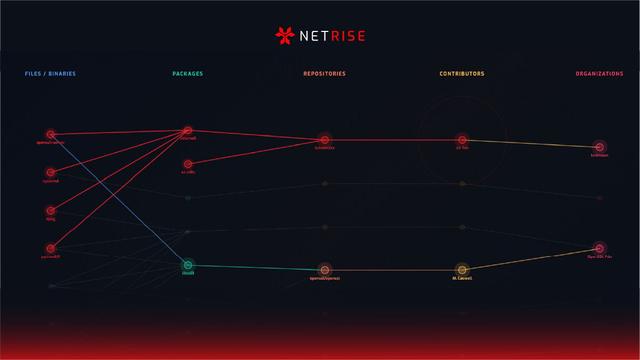
NetRise Provenance wants to track who writes your open source code after XZ backdoor scare
https://fed.brid.gy/r/https://nerds.xyz/2026/03/netrise-provenance-open-source-risk/
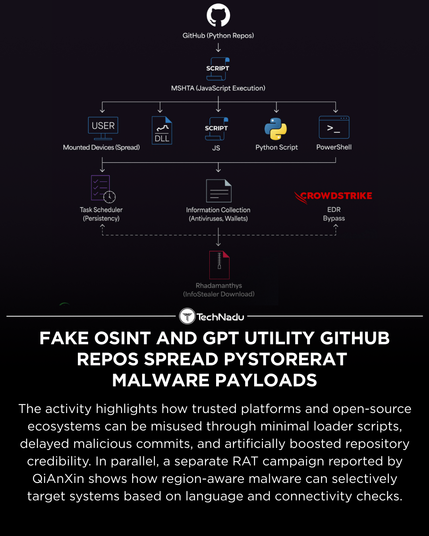
Researchers have documented a campaign abusing GitHub repositories themed as OSINT tools, GPT utilities, and developer resources to deliver PyStoreRAT, a modular, multi-stage remote access trojan.
The operation leverages delayed malicious commits, minimal loader stubs, reputation manipulation, and HTA-based execution to reduce early detection. In parallel, a separate RAT campaign demonstrates region- and language-aware targeting logic.
These cases underscore evolving tradecraft around trust abuse and script-based implants.
How are you adapting repository vetting and execution controls in your environment?
Source: https://thehackernews.com/2025/12/fake-osint-and-gpt-utility-github-repos.html
Engage in the discussion and follow TechNadu for measured infosec reporting.
#InfoSec #ThreatIntel #MalwareAnalysis #GitHubSecurity #OpenSourceRisk #TechNadu
An actively exploited GeoServer XXE vulnerability is prompting renewed discussion around breach readiness in public-sector and enterprise environments.
Experts note that unauthenticated flaws in widely deployed open-source platforms significantly increase exposure, especially where asset discovery and patch coordination are constrained.
Venky Raju, Field CTO at ColorTokens:
“The massive adoption of open-source software has significantly increased the attack surface of many enterprises, often without their knowledge. Unauthenticated vulnerabilities are particularly concerning because they bypass identity and application-level controls. The GeoServer vulnerability comes on the heels of a larger one called React2Shell (CVE-2025-55182), which scored a perfect 10 on the CVSS metric.
However, enterprises may not be able to patch servers quickly due to internal challenges, such as discovering affected assets, identifying affected applications, scheduling patch updates, etc. As an emergency measure, organizations should consider microsegmentation controls to isolate affected assets or zones with just enough policies to maintain business continuity while preventing lateral movement using commonly used techniques. The MITRE framework is an excellent guide for identifying the tactics hackers use to move laterally from the initially compromised system.”
How are teams handling containment when patching isn’t immediate?
Engage and follow @technadu for grounded infosec coverage.
#InfoSec #ZeroTrust #Microsegmentation #GeoServer #OpenSourceRisk #ThreatDetection #TechNadu
Sure, it was built with regulated industries in mind. But the Litmusverse works anywhere open source tools are used seriously.
From research teams to public sector organisations, it helps teams understand and reduce risk in their R package stack.
Because validation is not just about rules. It is about responsibility, reproducibility, and results.
Learn more: https://www.jumpingrivers.com/litmus/
#Litmusverse #OpenSourceRisk #RStats #SoftwareQuality #Validation
https://www.jumpingrivers.com/litmus/