Detroit Deathfest 2006
I Bands: Circle of Dead Children (PA) Summon (MI) Daath (GA) Decrypt (IN) Nocturnal Fear (MI) Saprogenic (MI) Unburied (VA) Ten Ton Dieselhead (MI) Darkness Undying (OH) Vein Of Lunacy (MI) Unregistered Sex Offender (OH) Goatswat (MI) Crucifist Venue: The 2500 Club Located in Downtown DetroitGoogle released a blog post on steps required to take ASAP, so that we are prepared for when quantum computers are readily available to crack current encryption [1]. I read it after I saw a video talking about this post, which as one might expect, was a bit alarmist. However, it is a real #cybersec #threat, and I've seen other sources mention, that #threatactors are starting to gather #encrypted #data in the expectation to readily #decrypt it in the near future. /1
An interesting lighting talk at #hacklu presenting a tool for Offline decryption of SCCM database secrets.
$19B Wiped Out in Crypto's Biggest Liquidation
https://decrypt.co/344038/morning-minute-19b-wiped-out-in-cryptos-biggest-liquidation-ever
#HackerNews #Crypto #Liquidation #Biggest #Losses #$19B #Decrypt #News
2030
It will be time to host his own server for family tchat and not to use official ones.
nothing to hipe, ok, but It is not the reason to let everyone reads and knows
https://www.techradar.com/vpn/vpn-privacy-security/the-eu-wants-to-decrypt-your-private-data-by-2030
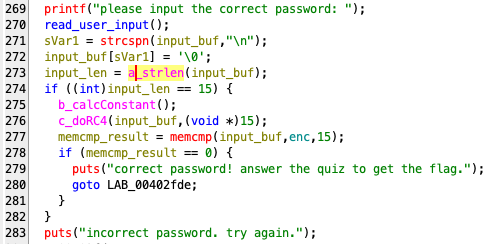
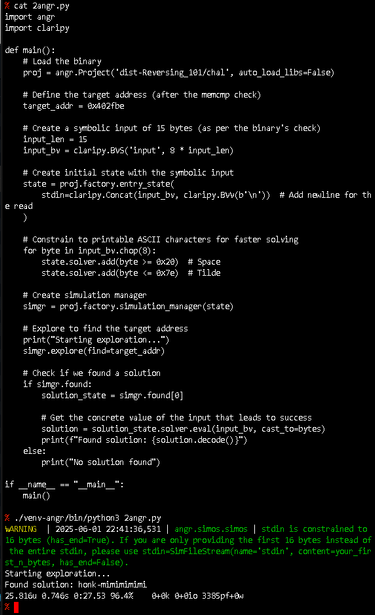
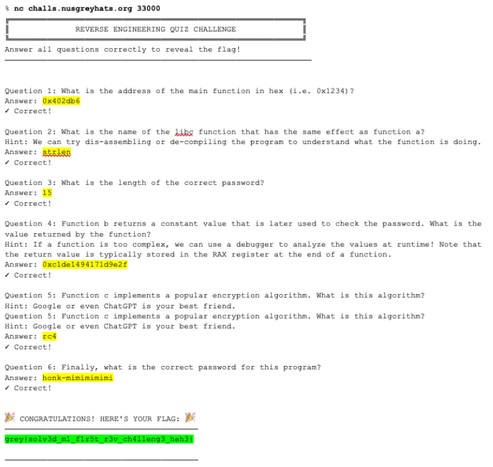
This weekend's GreyCatCTF had an interesting "Reverse 101" challenge in the "EZPZ" category. In "nc" a number of questions were asked on the binary, and the most interesting one was what a certain function did (RC4 encrypt) and what input is required to get the flag.
Besides ghidra & gdb, angr was very helpful here to get the plaintext for the RC4 encryption. See pictures for details.
#greycat #ctf #cybersecurity #angr #reverseengineering #rc4 #decrypt #ezpz #writeup #notawriteup #lazy
A̮åȃa̋áā Aăă Āa̰á Ãäa̡ạa̦ A̡a̦a̯a̰áȃ Aăa̋åȃảāa̰ǎã
🗣️🔥 **scream_cypher** — A cypher based on XKCD-3054
🅰️ Messages consist of all As with different letters
🦀 Available as both a CLI tool and a Rust library!
⭐ GitHub: https://github.com/icorbrey/scream_cypher
#rustlang #cypher #xkcd #encrypt #decrypt #library #commandline #meme