Unmasking The 64-bit Variant of the Infamous Lumma Stealer
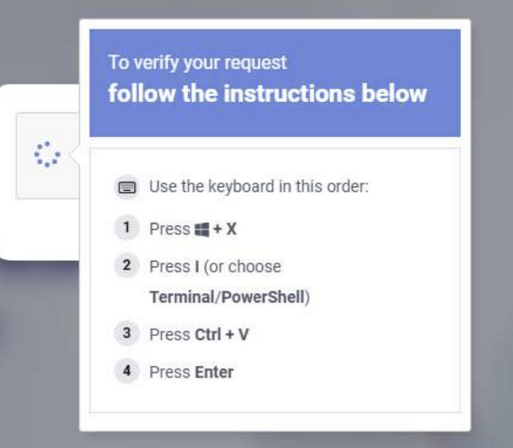
Gen Threat Labs has identified Remus, a new 64-bit infostealer attributed to the Lumma Stealer family, emerging after Lumma's takedown and the doxxing of its alleged core members. First campaigns date back to February 2026, with the malware switching from Steam/Telegram dead drop resolvers to EtherHiding and employing new anti-analysis checks. Remus shares multiple characteristics with Lumma including identical string obfuscation techniques, AntiVM checks, direct syscall/sysenter handling, indirect control flow obfuscation, and a unique Application-Bound Encryption bypass. The analysis details test builds labeled Tenzor from September 2025, representing a transitional step between Lumma and Remus. While maintaining Lumma's stealing arsenal for browser passwords, cookies, and cryptocurrency, Remus introduces blockchain-based C2 resolution via EtherHiding, additional anti-sandbox checks targeting analysis tool DLLs, and enhanced device fingerprinting capabilities.
Pulse ID: 69d61cf42af050999ace2be6
Pulse Link: https://otx.alienvault.com/pulse/69d61cf42af050999ace2be6
Pulse Author: AlienVault
Created: 2026-04-08 09:16:36
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BlockChain #Browser #Cookies #CyberSecurity #Encryption #EtherHiding #ICS #InfoSec #InfoStealer #LummaStealer #Malware #OTX #OpenThreatExchange #Password #Passwords #Steam #Telegram #Word #bot #cryptocurrency #doxxing #AlienVault