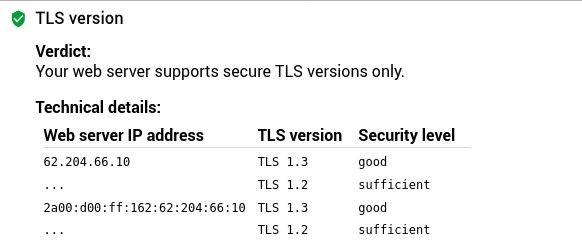
Microsoft to Discontinue Legacy TLS Versions in Exchange Online by July 2026
Microsoft is putting the brakes on outdated security protocols, announcing that it'll start blocking legacy TLS 1.0 and 1.1 connections to Exchange Online in July 2026 - so it's time to upgrade and stay secure! This move marks the end of an era for older clients that still rely on these outdated protocols.
#ExchangeOnline #TransportLayerSecurity #Tls10 #Tls11 #Microsoft