Two of the biggest heavyweight scam TTPs - malvertising and pig butchering - have combined. In our latest research, we track hundreds of investment‑scam campaigns using this one-two punch to target Japan and the wider Asia region.
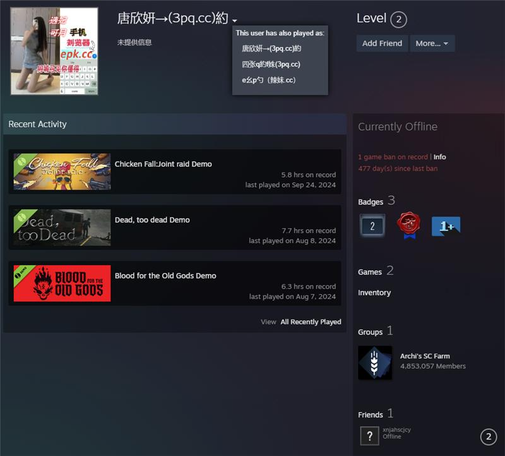
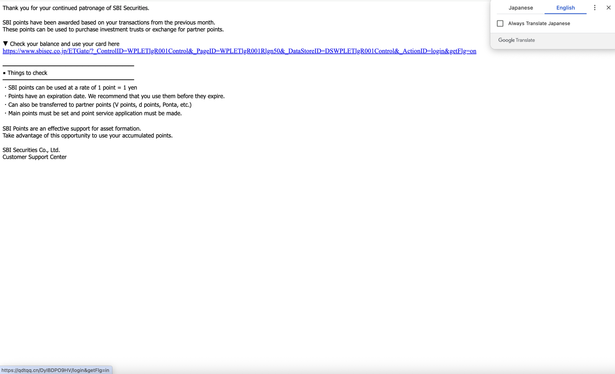
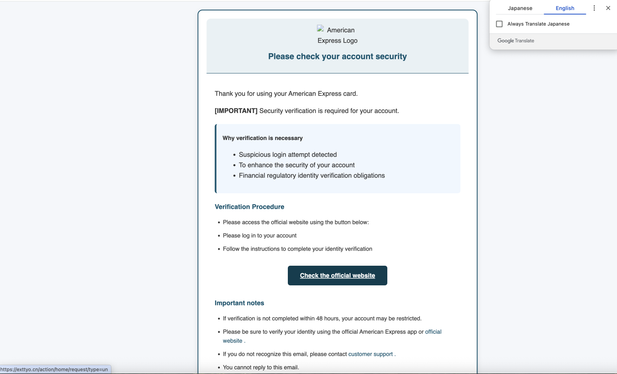
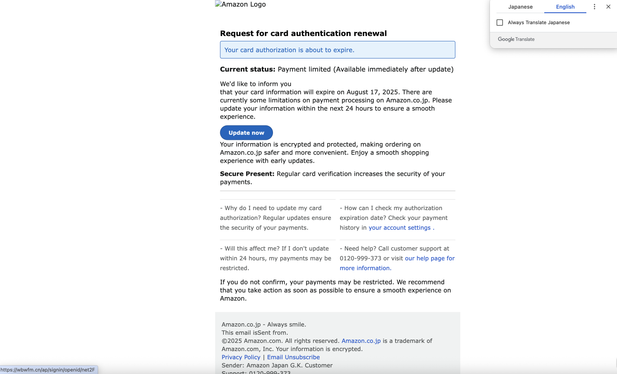
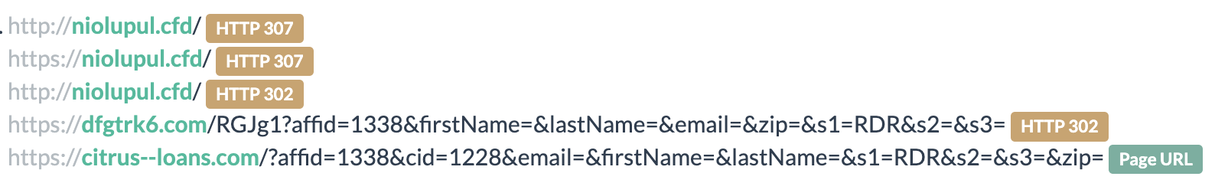
The hybrid approach kicks-off with malvertising ads that impersonate well‑known financial experts, funnel victims through lure sites on RDGA‑generated domains, before finally pulling them into messaging chats run by tireless AI‑style pig butcher bots. The result: an industrial‑scale long con, with individual victims reporting losses of up to ¥10M (~US$63k).
This model is reused across different campaigns and, by pivoting on DNS, we've so far been able to map out an ecosystem of over 23,000 domains.
In our latest blog we talk about our first‑hand experience going through the scheme, break down the entire flow, and share all the related IOCs: https://www.blogs.infoblox.com/threat-intelligence/banners-bots-and-butchers-an-automated-long-con-targeting-japan-asia-and-beyond/
#Infoblox #InfobloxThreatIntel #dns #threatintel #threatintelligence #malvertising #pigbutchering #rdga #dga #lookalikes #crypto #investment #scam #fraud #cybercrime #cybersecurity #infosec #Japan #Asia #AI