Recovery Scam Season: Second Time’s the Charm? 🎣
Fallen victim to online fraud and now seeing ads promising to get your money back—fast, guaranteed, no upfront fees?
⚠️ 📵 Yeah… about that.
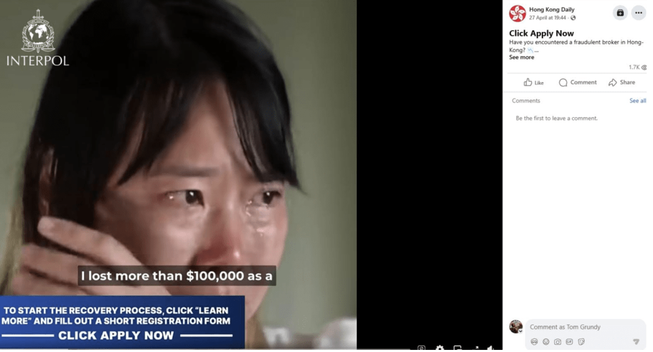
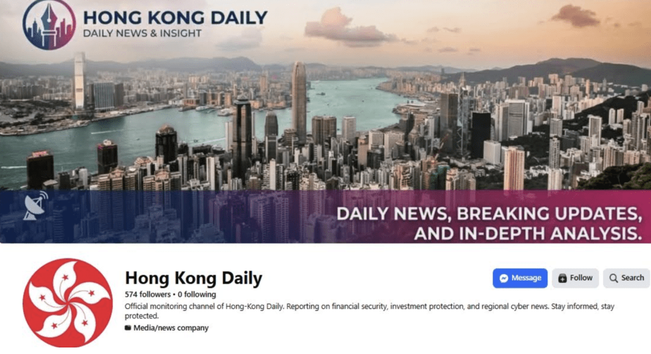
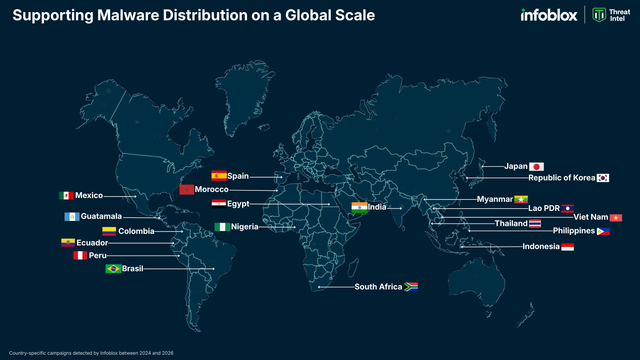
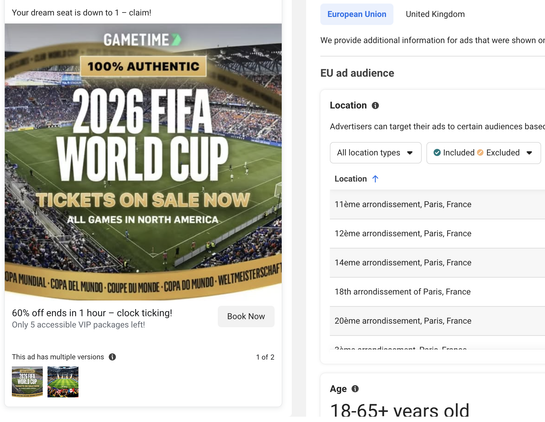
Victims around the world are being re-targeted by asset recovery scams impersonating INTERPOL, law enforcement agencies, law firms, and other trusted orgs. We've been tracking an actor deploying some slick AI-generated video ads boosted by fake news pages funneling users to polished lure sites promising miracle turnarounds. Talk about a sequel nobody asked for. 🎬
Here’s the playbook:
• 🎥 Fake ads pushing recovery services, often impersonating law enforcement →
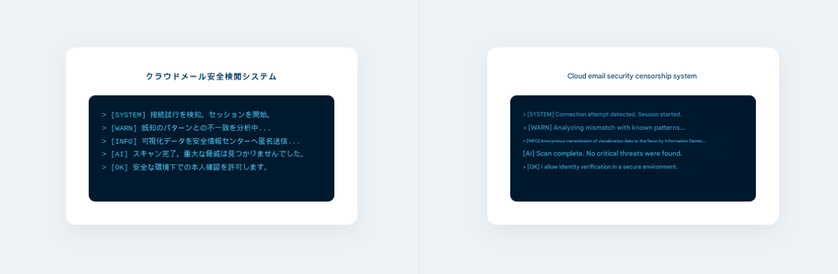
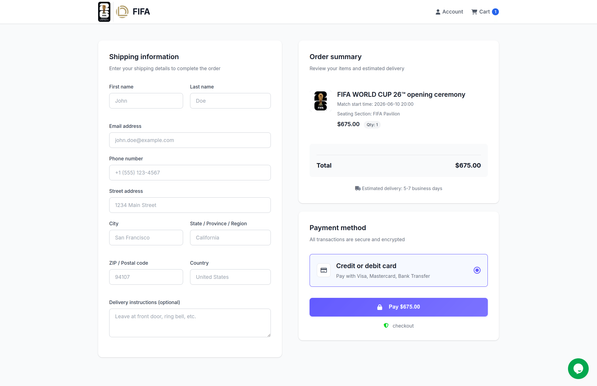
• 🌐 Lookalike recovery domains instructing victims to submit contact info →
• 📞 Outreach via Email, WhatsApp etc. →
• 🤝 Trust building + fake progress →
• 💳 “Processing” and "release" fees (and more… and more) until you're rinsed... again.
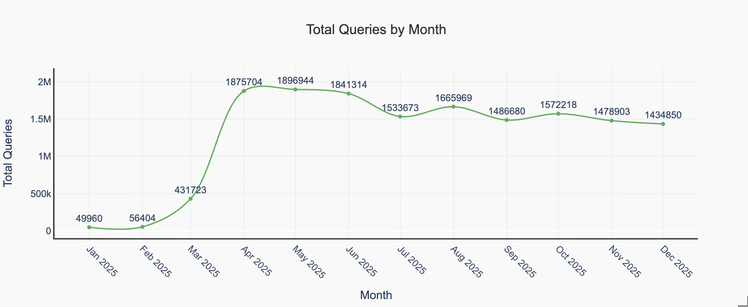
Through DNS telemetry, we’ve been tracking this cluster for months—connecting the dots across campaigns long before takedowns hit timelines.
META recently pulled some INTERPOL-themed ads after Hong Kong media coverage—but plenty remain. The Russian-speaking actor behind this is pivoting fast, spinning up new brands, domains, and “legal services” at scale.
Recent examples:
⛔ europolhelp[.]live
⛔ recovery-protocol[.]net
⛔ fbi-support[.]live
⛔ baseinfo[.]biz
Still waiting on our recovered funds. Until then, we’ll keep tracking—because while threat actors evolve, DNS remembers.🧠
#ThreatIntel #Scam #CyberSecurity #DNS #Infoblox #crypto #cybercrime