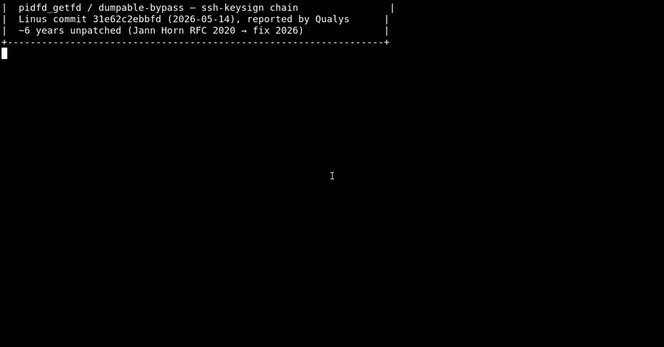
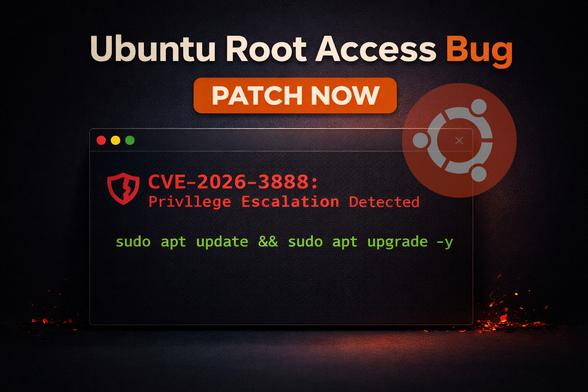
Researchers disclosed CVE-2026-46333, a Linux kernel flaw present since 2016 that enables local users to access sensitive files and execute commands as root. 🐧
Qualys said Debian, Fedora and Ubuntu default installs are affected, while admins are urged to patch kernels and rotate exposed SSH keys. 🔑
🔗 https://thehackernews.com/2026/05/9-year-old-linux-kernel-flaw-enables.html
#TechNews #Linux #Kernel #CVE202646333 #CVE #Cybersecurity #Qualys #Ubuntu #Debian #Fedora #OpenSource #FOSS #Security #Exploit #Infosec #SysAdmin #Privacy #SSH #Admin