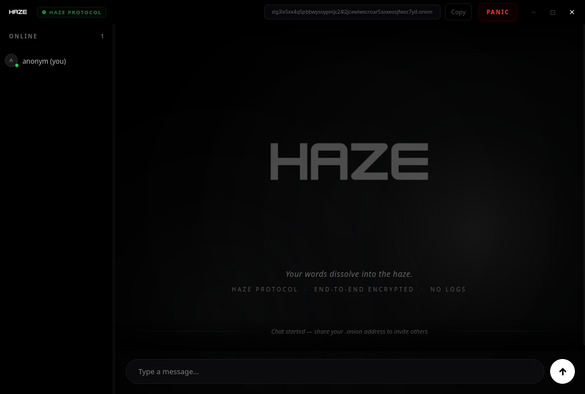
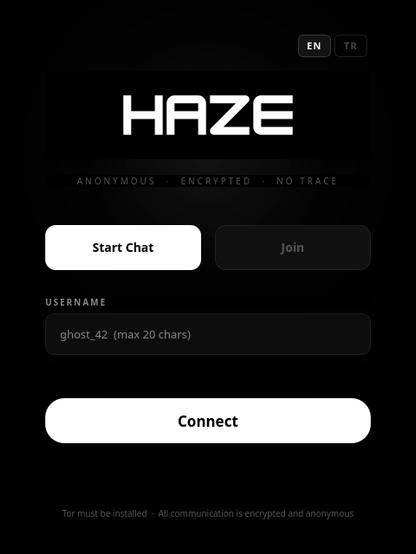
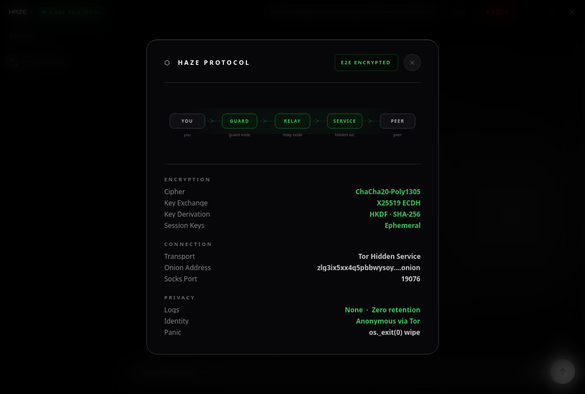
Haze: A decentralized, open-source P2P group chat with E2EE routing entirely through Tor. Maximum privacy, zero trace.
https://haze.berkkucukk.com
#kalilinuxtools #informationsecurity #ethicalhacker #pentesting #ubantu #bugbounty #github #githubuniverse #hacking #hacking_or_secutiy #WebPentest #webpentest #decryption #ddosattak #networkattacktool #networkattack #WhatWeb #metasploit #nmap #burpsuite #bruteforce #informationgathering #hackingtools #vulnerability #kalilinux