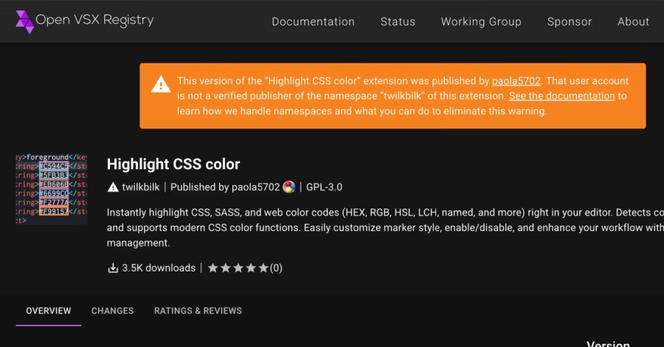
🕵🏻♂️ [InfoSec MASHUP] - This week's news cycle handed us the usual parade of breaches, arrests, and patch-your-stuff urgency — but if you squint at the #Malware section long enough, a more uncomfortable story emerges. #SAP-related npm packages backdoored with a credential stealer. A popular #PyPI package hijacked via a forged signed release pushed through a compromised GitHub Actions workflow. Seventy-three "sleeper" extensions quietly sitting in #OpenVSX, waiting. The common thread: attackers aren't breaking down the front door anymore. They're walking in through the tools developers use every day, often with a valid signature and a clean commit history.
What makes this particularly fun — in the way a slow-motion disaster is fun — is that the blast radius isn't just the developer who ran pip install. It's every downstream user, every CI/CD pipeline, every AI coding agent that helpfully executed the preinstall hook without asking questions. The supply chain isn't a niche threat vector reserved for nation-state ops anymore. It's where commodity attackers are increasingly playing, because it scales beautifully and the detection gap remains embarrassingly wide.
→ Week #18/2026 also covers: Supply chain attackers found the path of least resistance, #OpenSSH patched a bug older than most junior devs, and #Europe is done pretending U.S. #cloud is a neutral choice.
Full issue 👉 https://infosec-mashup.santolaria.net/p/infosec-mashup-18-2026-shinyhunters-week-off-they-didn-t-take-one
If you find it useful, subscribe to get it in your inbox every weekend 📨 #infosecMASHUP #cybersecurity #infosec #threatintel #AI