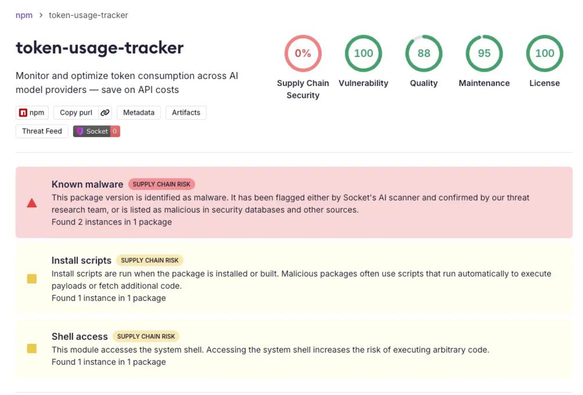
Active supply chain attack across NPM, PyPI, and Crates. io
npm, PyPI, Crates.io 등 주요 패키지 생태계에서 TrapDoor라는 암호화폐 탈취 악성코드가 포함된 34개 패키지와 384개 버전이 발견되어 활발한 공급망 공격이 진행 중이다. 공격자는 암호화폐 지갑, SSH 키, 클라우드 자격증명, GitHub 토큰 등 민감 정보를 탈취하며, 보안 연구팀 Socket은 평균 5분 27초 내에 악성 패키지를 탐지했다. 이 공격은 AI, DeFi, 보안 개발자들을 주요 타깃으로 삼고 있어 즉각적인 대응과 주의가 필요하다.
https://twitter.com/socketsecurity/status/2058565153138844043
Socket (@SocketSecurity) on X
🚨 BREAKING: Active supply chain attack across npm, PyPI, and Crates.io. Socket detected TrapDoor, a crypto stealer campaign hitting 34 malicious packages and 384 versions and artifacts, with attackers repeatedly pushing new releases across ecosystems. TrapDoor targets