Lots of updates in March! Many of the games (including word search / picture puzzles) have been updated to work better on small screens and lots of background changes to improve download speed and simplify maintenance! More details on the home page https://ssjx.co.uk
🥳 New JavaScript Database (JSDB) release
• Fix: Now properly handling array indices on `JSTable.PERSIST` events in the `keypath` property that’s passed to the event handler.
Just noticed that the pretty keypaths of the JavaScript deltas written to the append-only log were ignoring array indices while playing with a new database introspection call I’m adding to the Kitten Interactive Shell (REPL) and fixed it.
I’ll be updating Kitten shortly to use this version of JSDB and I haven’t forgotten my promise to record a little video of the new Kitten Introspection API.
Enjoy!
💕
https://codeberg.org/small-tech/jsdb#readme
#JavaScriptDatabase #javascript #database #JSDB #SmallTech #SmallWeb #NodeJS
RE: https://bsky.app/profile/did:plc:6gbm7hkapyhjt2jghosdzwv2/post/3migjjuhcwd2y
https://www.forbes.com/sites/phoebeliu/2026/03/31/openai-graveyard-deals-and-products-havent-happened-openai/ #OpenAI #HackerNews #ngated
Just made a little correction to the JavaScript Database (JSDB) Table Events section:
Previously, the example that listens for the JSTable.PERSIST event was erroneously stating that the table was deleted when the `type` property in the event handlers parameter object was JSTable.DELETE. It now correctly states that the value at `keypath` was deleted.
I also documented the JSTable.PERSIST types so they wouldn’t be confused with the JSTable event types (persist and delete; the latter of which does actually signal that the table – i.e., the append-only JavaScript log – was deleted.
https://codeberg.org/small-tech/jsdb#table-events
#SmallWeb #SmallTech #JavaScript #database #JSDB #documentation #events #fix
From Inbox to Intrusion: Multi‑Stage Remcos RAT and C2‑Delivered Payloads in Network
This multi-stage fileless Remcos RAT attack leverages a phishing-delivered JavaScript dropper to trigger a reflective PowerShell loader that executes payloads entirely in memory. The infection chain utilizes obfuscation techniques like rotational XOR and Base64 encoding to reconstruct .NET payloads, significantly reducing the disk-based detection footprint. Stealth is maintained by using aspnet_compiler.exe as a LOLBin to proxy malicious execution and dynamically retrieving the final payload from a remote C2 server.
Pulse ID: 69cd1ac8518646002a1a0fbc
Pulse Link: https://otx.alienvault.com/pulse/69cd1ac8518646002a1a0fbc
Pulse Author: AlienVault
Created: 2026-04-01 13:16:56
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#ASPNet #ASPNet_Compiler #CyberSecurity #InfoSec #Java #JavaScript #NET #OTX #OpenThreatExchange #Phishing #PowerShell #Proxy #RAT #Remcos #RemcosRAT #bot #AlienVault
You Can Use Same Variable Name TWICE?!
🔥 NO WAY! Destructuring allows DUPLICATE variable names in the same statement! const {a, a} = obj is VALID JavaScript! Last one silently wins. ESLint doesn't catch this by default. Tag a dev who needs to see this!
#javascript #javascripttricks #codingchallenge #destructuring #javascriptes6 #javascriptquiz #javascriptweird #javascriptwtf #javascriptbugs #codinginterview #codingtips #javascriptshorts
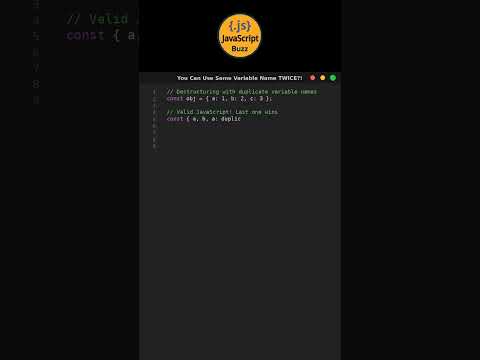
You Can Use Same Variable Name TWICE?! #codingchallenge
Claude Code Unpacked : A visual guide (ccunpacked.dev)
Those of you who follow me for some time know that I have many creative fields I like and I change between them. So, one of them is game development.
Currently I re-create Super Mario Bros. 3 with the Phaser library in JavaScript. It's fun and I learn more about how Toshihiko Nakago coded Mario's movement.
With those game re-creations I improve the mechanics of my own games.
I know, you should stick to one theme to not confuse your followers. Do you would like me to stick to one area like generative art, drawing, gamedev or sculpting?
Please let me know in a reply.
#game #javascript #supermario #phaserjs #nintendo #games #art #mastoart #fediart #noai #code #artwork #minimalism #creativecoding #random #arts #artistsonmastodon
(animation / remake)
Hindi mo kailangan ng JavaScript para mag-truncate ng text.