#GnuPG 2.2.54-freepg has been released.
It contains all the latest bug fixes from upstream GnuPG, plus the usual FreePG patches.
Release Notes
=============
## Noteworthy changes in version 2.2.54-freepg (2026-04-24)
* No FreePG-specific changes.
https://gitlab.com/freepg/gnupg/-/releases/gnupg-2.2.54-freepg
Upstream's release notes follow.
-------------
## Noteworthy changes in version 2.2.54 (2026-04-20)
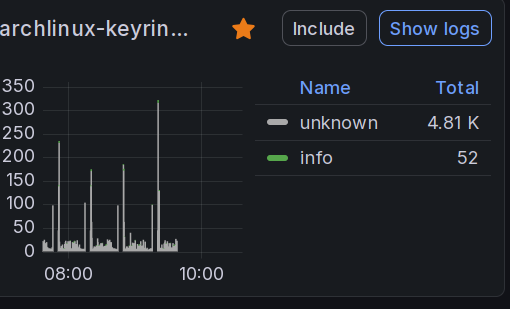
* gpg: Fix an edge case in --refresh-keys. [T8197]
* gpgsm: Add a certificate chain check for de-vs compliance.
[T8188]
* gpgsm: Show rsaPSS certificates as de-vs compliant in listings.
[T8222]
* agent: Accept a trustlist with a missing LF at the end. [T8078]
Release-info: https://dev.gnupg.org/T8170