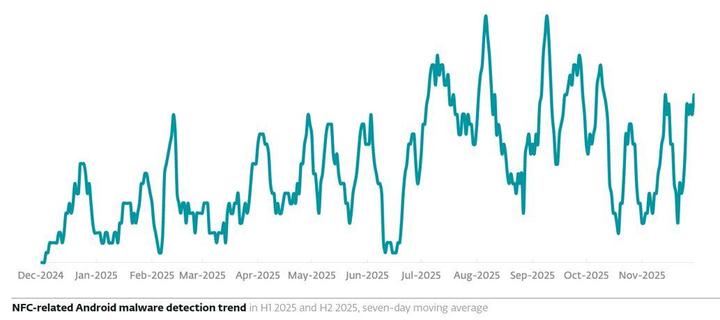
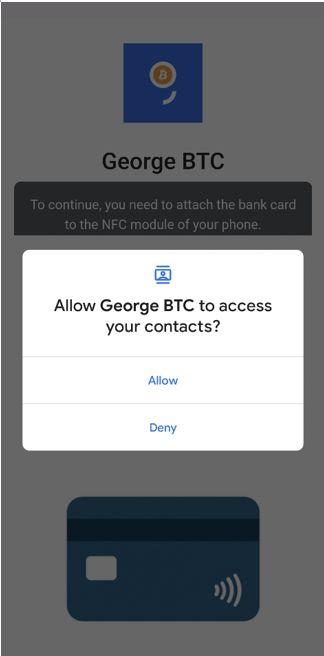
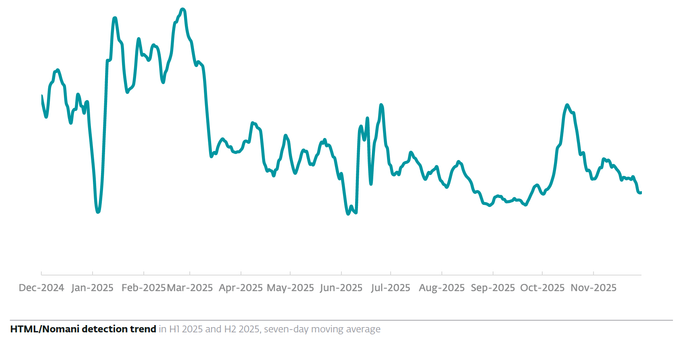
#NGate has demonstrated its relevance and is now enhanced with contact-stealing functionality. ESET researchers believe that this feature is designed to lay the groundwork for future attacks.
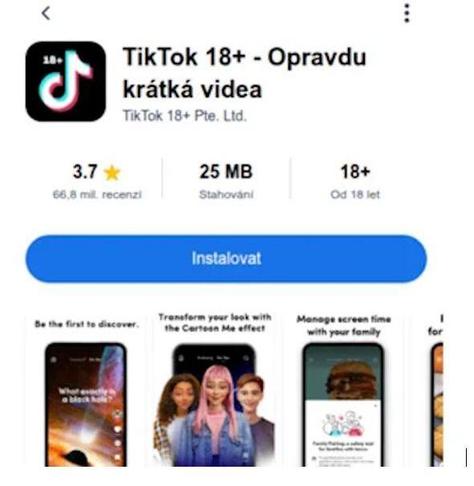
An NGate-based malware adapted for Brazil, #PhantomCard, targets banking clients via fake #Android apps that claim to improve security and privacy, distributed on pages featuring fabricated positive reviews.
And #RatOn combines RAT-like features with relay functionality, showcasing the determination of threat actors to evolve the methods of compromise. It’s distributed via fraudulent ads and apps, with the language targeting Czech and Slovak users.
Attackers remain faithful to tried-and-tested methods like #phishing calls and messages, while increasingly relying on psychological manipulation and #social engineering rather than exploiting just the technological aspect of NFC.
Read more about the evolution of NFC threat landscape in the latest #ESETThreatReport https://web-assets.esetstatic.com/wls/en/papers/threat-reports/eset-threat-report-h22025.pdf