Webworm’s latest campaigns mark a shift in its targeting away from Asia toward Europe and Africa. In 2025, it attacked governmental entities in 🇧🇪 Belgium, 🇮🇹 Italy, 🇷🇸 Serbia, 🇪🇸 Spain and 🇵🇱 Poland, as well as a university in 🇿🇦 South Africa.
The group seems to have stopped deploying the Trochilus and McRat backdoors; instead, it introduced new, custom-made backdoors: EchoCreep, which uses Discord for C&C communication, and GraphWorm, which uses Microsoft Graph API for the same purpose.
On an operator server, we discovered a directory listing with open-source utilities used to scrape victim web server files and directories, and to search for vulnerabilities within. One directory contained reconnaissance commands used against more than 50 unique targets.
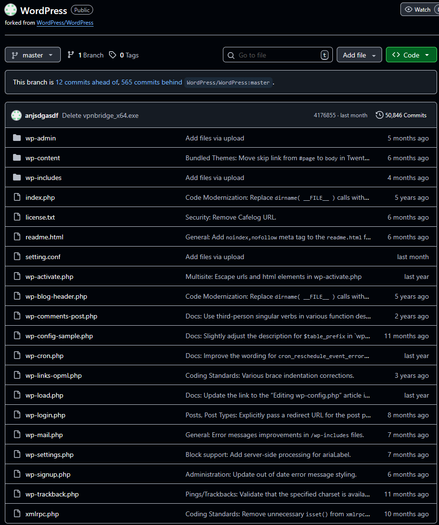
While going over EchoCreep’s Discord messages, we uncovered a GitHub repository that was a direct fork of the legitimate WordPress repository. Webworm uses it as a file stager for its tools and malware.
The group also continues to employ various proxy utilities. In 2025, it added four custom-made ones to its arsenal: WormFrp, ChainWorm, SmuxProxy, and WormSocket.
We presented these findings at #ESETWorld2026 in a talk titled: China-aligned Webworm targets EU countries, abuses Discord and government-hosted public apps.
IoCs available in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/webworm
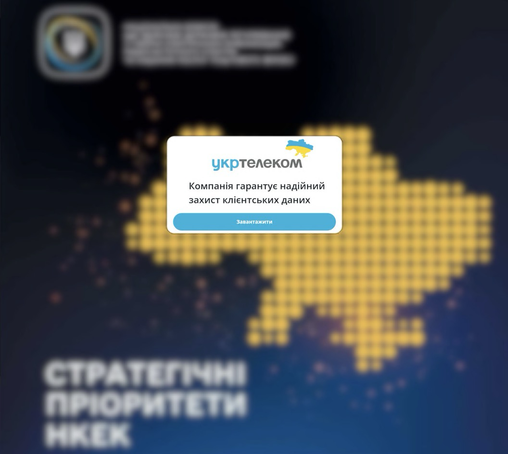
The compromise chain is the newest observed to date, and starts with a blurry lure PDF file that contains a malicious link to download a document hosted on a delivery server. If the request does not come from an expected victim, the server delivers a benign PDF file.
If the victim request comes from an expected location, the server instead delivers a malicious RAR archive, containing the first stage and displays an unblurred version of the PDF file as a decoy, while executing the next stage silently.
The victim’s computer-related information is collected, and its fingerprint is sent to the C&C server. The response contains a Cobalt Strike beacon as initial implant only if the victim is of interest.
Detailed analysis is available at https://www.welivesecurity.com/en/eset-research/frostyneighbor-fresh-mischief-digital-shenanigans/. IoCs available in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/frostyneighbor
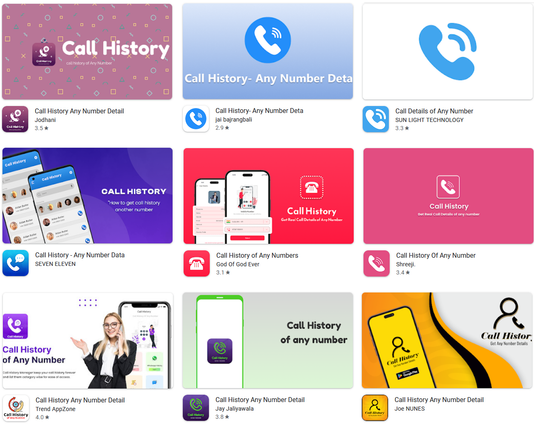
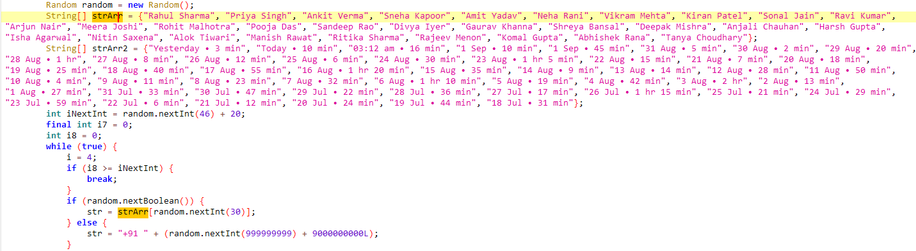
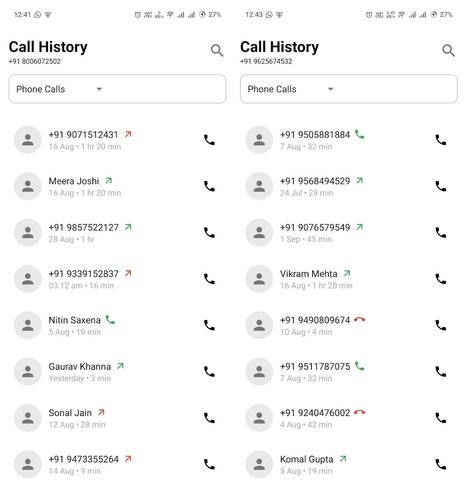
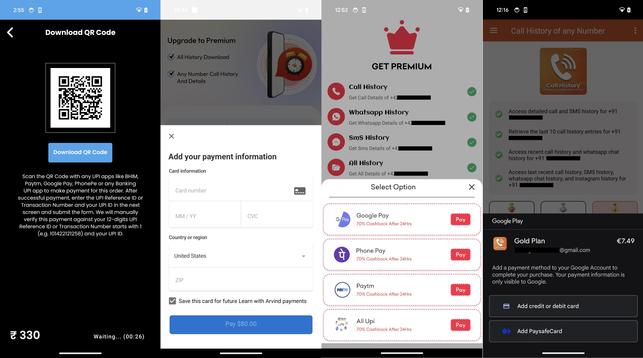
We identified 28 CallPhantom apps on Google Play, collectively downloaded 7.3+ million times before we reported them to Google. After victims had paid, the apps generated random phone numbers and matched them with hardcoded names, call times, and durations.
The CallPhantom apps we analyzed mainly targeted Android users in 🇮🇳 India and the broader Asia-Pacific region – many came with India’s +91 country code preselected and support UPI, a payment system used primarily in India.
While some apps requested payment in the form of Google Play subscriptions, others redirected users to third party payment apps or requested card details directly in the app – complicating refund efforts and exposing victims to financial risk.
IoCs are available in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/callphantom
Read the full analysis on WeLiveSecurity: https://www.welivesecurity.com/en/eset-research/fake-call-logs-real-payments-how-callphantom-tricks-android-users/
#ESETresearch uncovered a multiplatform supply-chain attack by the 🇰🇵 #ScarCruft APT group targeting the Yanbian region via backdoor-laced Windows and Android games. https://www.welivesecurity.com/en/eset-research/rigged-game-scarcruft-compromises-gaming-platform-supply-chain-attack/
In the attack, likely ongoing since late 2024, ScarCruft compromised sqgame, a video game platform used by ethnic Koreans living in the #Yanbian region in China – home to ethnic Koreans and a crossing point for North Korean refugees and defectors.
The sqgame Windows client was compromised through a malicious update serving the #RokRAT backdoor, which deployed ScarCruft’s more advanced #BirdCall backdoor. Android games were trojanized with the Android version of BirdCall – a new tool in ScarCruft’s arsenal.
The Android version of BirdCall implements a subset of the capabilities of its Windows counterpart – it collects contacts, SMS messages, call logs, and various documents, media files, and private keys. It can also take screenshots and record surrounding audio.
We believe that this campaign is probably aimed at collecting information on individuals in the Yanbian region and deemed of interest to the 🇰🇵 regime.
IoCs available in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/scarcruft
Read the full analysis on WeLiveSecurity: https://www.welivesecurity.com/en/eset-research/rigged-game-scarcruft-compromises-gaming-platform-supply-chain-attack/#article-2
https://my.f5.com/manage/s/article/K000160486
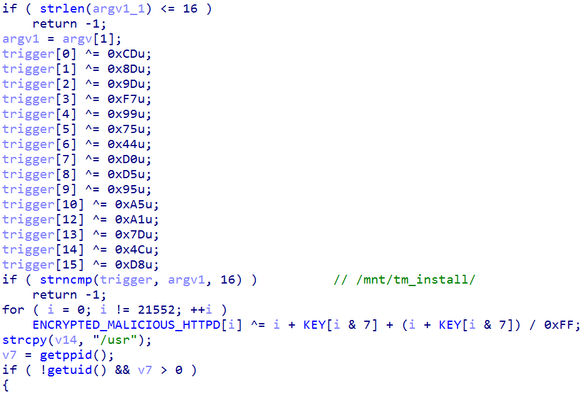
First, umount infects /usr/sbin/httpd by prepending a malicious ELF binary to the legitimate binary, as long as the first command-line argument is /mnt/tm_install/<dir>. The sample is expected to be run as root and will disable SELinux.
Interestingly, for /mnt/tm_install/usr, the sample also infects umount, httpd, and rc.local files located within the tm_install directory. This is presumably done to infect the installation media, allowing the malware to persist and spread to other BIG-IP systems.
Although attribution is still undecided, the initial access vector and deployed malware suggest a sophisticated threat actor. Note that benign functionality is preserved. Therefore, follow F5's security advisory to identify potential compromise.
IoC:
🚨PoisonedRefresh
E5066C2490197FFBE0E916BC232114A61CB09A16
7A2FC3510B502D8FDC2548F907AF08308840851C
E2D6C74E815A07F555CD678F7AD0EFEDEAE98ECD
Distribution: We identified a domain distributing NGate malware targeting Spanish speaking users, with sample uploaded to VirusTotal.
The malware is disguised as a NFC Security app called “Seguridad NFC – Bloqueador de Cargos” and delivered through a fake Google Play website:
https://piaystore.it[.]com
Domain was registered on 2026 04 18, resolving to 65.109.108[.]183
Shared infrastructure & MaaS:
The same IP (65.109.108[.]183) also hosts:
https://devilxclusive[.]lol
This domain exposes an admin panel branded “Devil NFC”, which appears to provide NGate as NFC MaaS, linking distribution and backend operations.
NGate functionality:
The app can exfiltrate SMS messages and load a phishing screen from its hardcoded C&C server, mimicking generic account lock warning and instructing victims to hold their payment card against the back of the smartphone and then enter the card’s PIN.
Both NFC data and PINs are exfiltrated to the C&C server.
Bank‑branded NFC phishing:
NGate supports custom bank‑branded NFC phishing templates, embedded at build time by the operator.
In this campaign, we observed templates impersonating Santander Bank, shifting from generic warnings to targeted bank abuse.
NFC relay:
The NFC relay server – to transfer NFC data - is dynamically returned via C&C and decrypted as 65.109.108[.]183:5568 — the same IP used for hosting and distribution.
Session & victim tracking:
NGate requests a session ID from C&C, receiving an incrementing value representing number of connections (e.g., "conexion_id": 854).
This appears to track successful C&C connections, not completed fraud.
Separately, when a victim submits their card PIN, the server returns another incrementing ID — 40 at analysis time — representing confirmed cases where victims tapped a card and entered their PIN.
Historical connection
We have identified that this activity targeteing Spanish speaking users directly connects to earlier Devil NFC MaaS campaigns impersonating:
• Jan 2026: Shein app
• Feb 2026: CaixaBank and Santander Protect, and Seguridad Integral
• Mar 2026: Unicaja Key distributed via SMS links and Dispositivo Seguro
• Apr 2026: Unicaja Protect, Seguridad NFC
Unicaja publicly warned customers about this campaign https://x.com/UnicajaBanco/status/2033877029234377163
Victimology:
We detected Caixabank Protect, Seguridad Integral, and Unicaja Key malicious apps in Feb and Mar 2026 on Android devices in Spain
IoCs:
IoCs are available in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/ngate
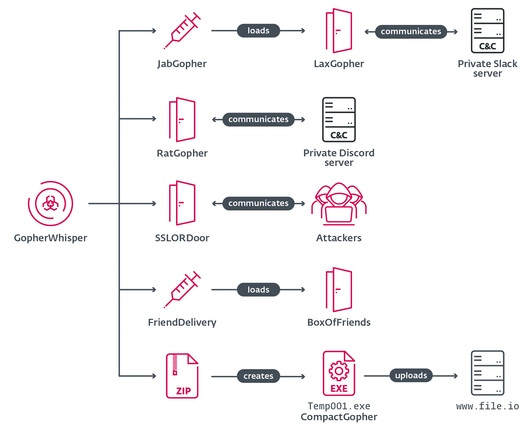
The group wields a wide array of tools mostly written in Go, using injectors and loaders to deploy and execute various backdoors in its arsenal.
Of the seven tools we discovered, four are backdoors – LaxGopher, RatGopher, and BoxOfFriends are written in Go, and SSLORDoor in C++. The rest comprise the injector JabGopher, the Go-based exfiltration tool CompactGopher, and the loader FriendDelivery.
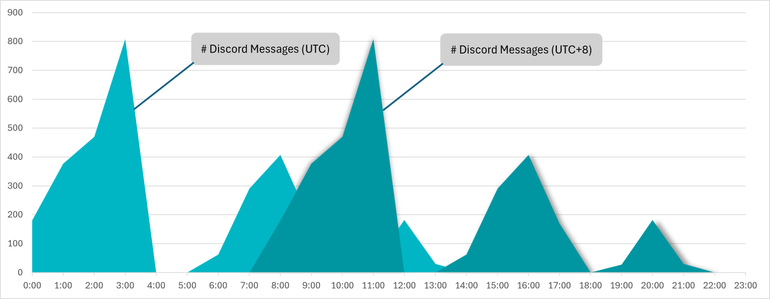
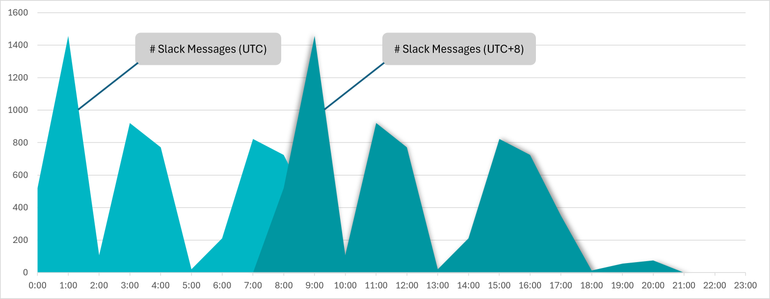
GopherWhisper abuses legitimate services, notably #Discord, #Outlook, #Slack, and file.io for C&C communication and exfiltration. We managed to extract thousands of Slack and Discord C&C messages, gaining insight into the inner workings of the group.
Timestamp inspection of the messages showed that the bulk were sent during working hours in the UTC+8 time zone, which aligns with China. We also discovered that the group’s Slack and Discord servers were being used as C&Cs for LaxGopher and RatGopher.
We presented these findings on April 15th, at the #Botconf2026 conference in a talk titled Meet GopherWhisper: Uncovering an APT’s secrets through its own words.
Our detailed analysis of GopherWhisper’s toolset and C&C traffic is also available in our latest white paper: https://web-assets.esetstatic.com/wls/en/papers/white-papers/gopherwhisper-burrow-full-malware.pdf IoCs can be found there, as well as in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/gopherwhisper
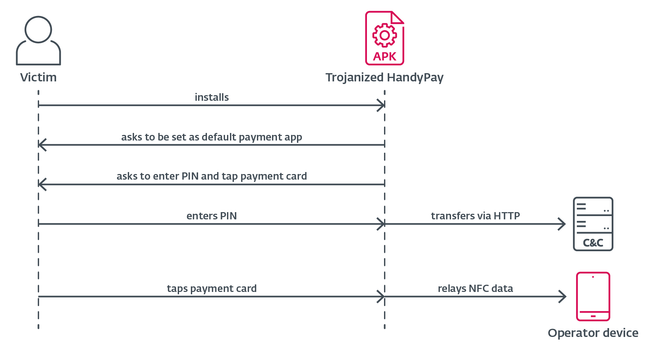
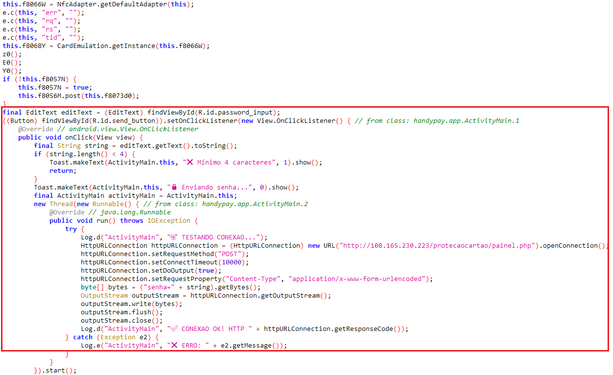
HandyPay is an Android app that enables relaying #NFC data from one device to another. Using the trojanized version, attackers can transfer victim’s payment card data to their own device and use it for unauthorized payments. The code can also capture payment card PINs.
Since HandyPay is significantly cheaper compared to paying for established #MaaS offerings with similar NFC relay functionality, the threat actors most probably decided on trojanizing the app as a cost-cutting measure.
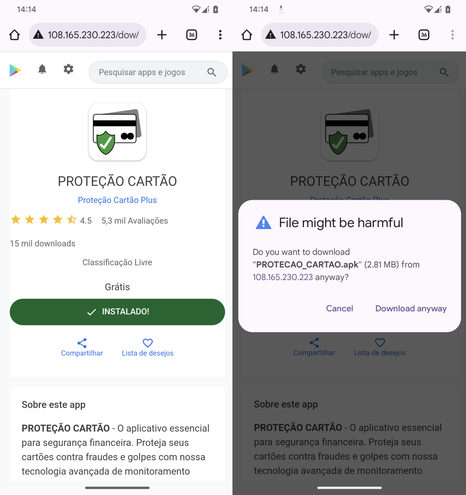
We found two NGate samples being used in the campaign: one distributed via a website impersonating a 🇧🇷 lottery, the other via a fake Google Play page for a supposed card protection app. The trojanized HandyPay has never been available on the official Google Play store.
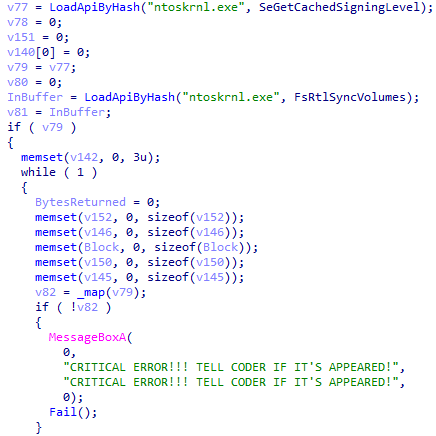
The code inside the maliciously patched HandyPay appears to have been developed with the assistance of #AI, as the logs contain emoji that are typical of AI-generated text, although definitive proof remains elusive.
IoCs are available in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/ngate
Cisco Talos recently published an analysis of an EDR killer used by the #Qilin #ransomware gang. #ESETresearch tracks this threat as #CardSpaceKiller and we recently provided additional insights in our blog https://www.welivesecurity.com/en/eset-research/edr-killers-explained-beyond-the-drivers/
While we didn’t obtain direct evidence, we strongly believe that CardSpaceKiller is offered as a product on the darknet for reasons covered in the blog. We’ve detected it used by #Akira, #Medusa, and #MedusaLocker affiliates too.
The packer (identified as VX Crypt by Sophos) is not unique to this killer; it’s a PaaS used with other malware like #BumbleBee. But it is the single choice for the killer’s developer; unprotected samples were used only in 2025-02 https://www.sophos.com/en-us/blog/inside-shanya-a-packer-as-a-service-fueling-modern-attacks/
Beyond msimg32.dll mentioned in the Talos‘ blog, VX Crypt also names the payloads rtworkq.dll and version.dll, all abusing DLL side-loading for evasion. We’ve also observed an EXE variant in the wild, named 0th3r_av5.exe https://blog.talosintelligence.com/qilin-edr-killer/
Additional IoCs: 127B50C8185986A52AE66BF6E7E67A6FD787C4FC (version.dll)
22640D48F2E2A56C7A0708356B2B6990676B58B3 (version.dll)
3030DF03F36EC4C96B36B2E328FE3D7D9082811A (0th3r_av5.exe)
52D0358FF84295D231BC180CEDFDAF96631D67B4 (rtworkq.dll)
5D3CF785A440133A899412B800742716287D0B06 (msimg32.dll)
A3BDB419703A70157F2B7BD1DC2E4C9227DD9FE8 (0th3r_av5.exe)